EMEA Monthly Talos Update
15:30
Join Hazel, Martin and special guests as they discuss social engineering and the true impact of AI on cybersecurity.
Related Videos
In Security
-
Play video Build resilience
Build resilience
Unlock end-to-end visibility from edge to app for faster troubleshooting. Expand your zero trust reach confidently with a unified approach.
0:32
-
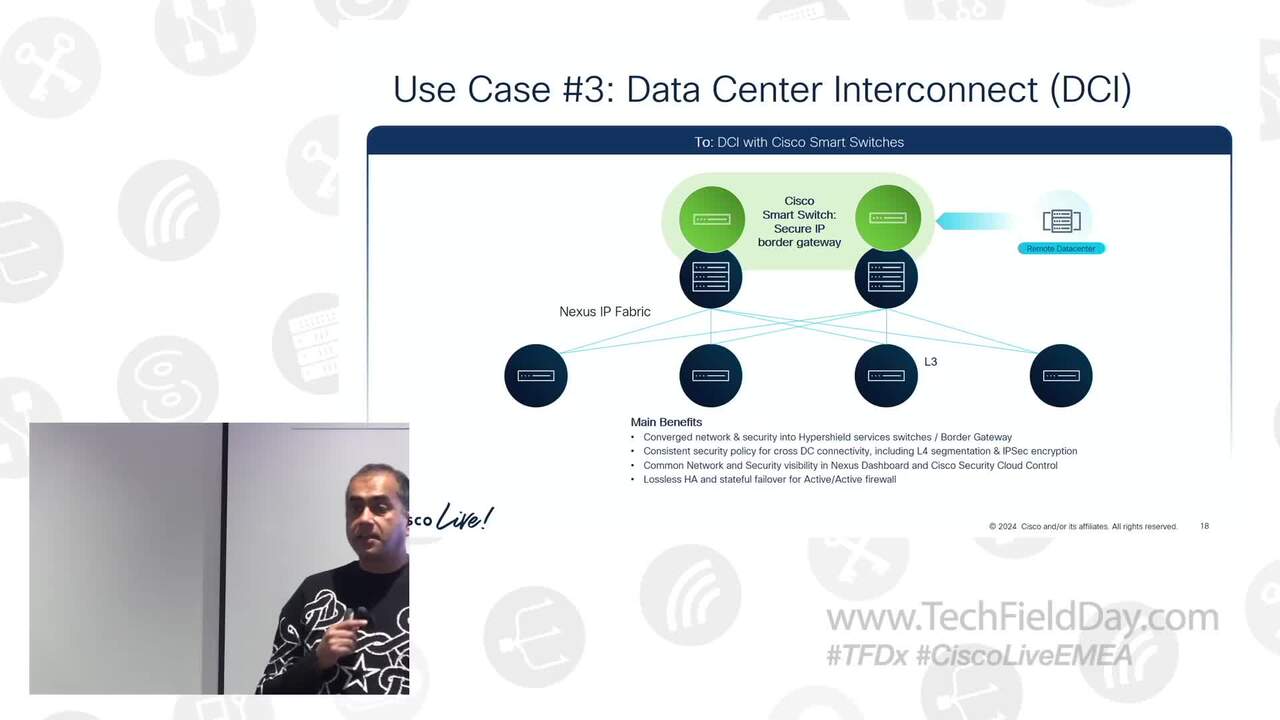
Play video Cisco Nexus Smart Switch and Hypershield Integration
Cisco Nexus Smart Switch and Hypershield Integration
In this session, our experts introduce a new family of Nexus data center Smart Switches with DPUs, enabling stateful services to be embedded directly into the data center fabric at scale.
1:02:40
-
Play video Unveiling the new Universal ZTNA
Unveiling the new Universal ZTNA
Cisco Universal ZTNA modernizes VPN, protects identities and builds resilience.
1:58
-
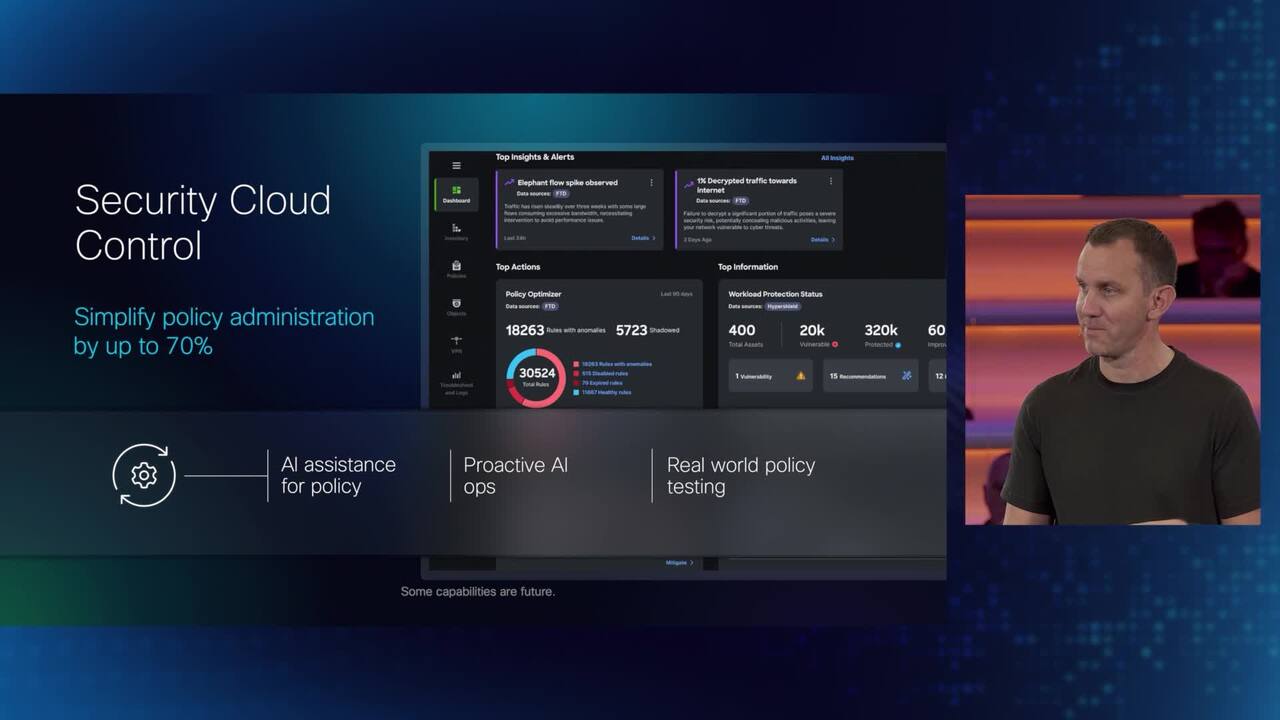
Play video Unified management with Security Cloud Control
Unified management with Security Cloud Control
Hear Cisco Security CTO, Craig Connors explain how Security Cloud Control delivers unified management for Hybrid Mesh Firewall
2:23
-
Play video Protect identities
Protect identities
Discover accounts that may be at risk, or pose a risk. Use phishing-resistant multi-factor authentication (MFA) on all apps—legacy and modern ones—in a way that frustrates attackers and not users.
0:31
-
Play video How United Airlines Modernizes with Cisco SD-WAN | How I Cisco
How United Airlines Modernizes with Cisco SD-WAN | How I Cisco
Shawn Walker of United Airlines shares how Cisco SD-WAN powers secure, agile connectivity across 600+ locations, improving performance and enabling a cloud-first approach.
0:57