-
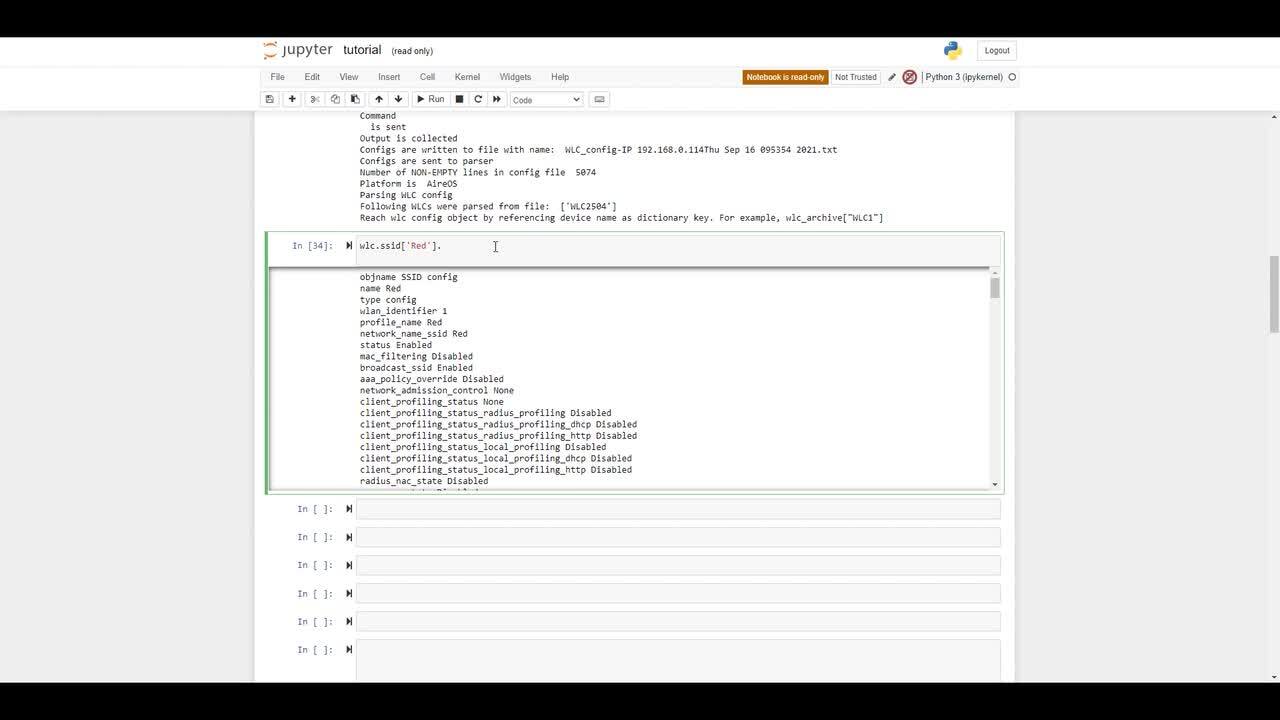
How to Python-ize the data from wireless network
Cisco Wireless LAN Controller configuration files contain a lot of useful information. But basic Python knowledge with the WLC pythonizer tool will allow anyone to reach new heights in configuration analysis and wireless network operational data.
20:53
-
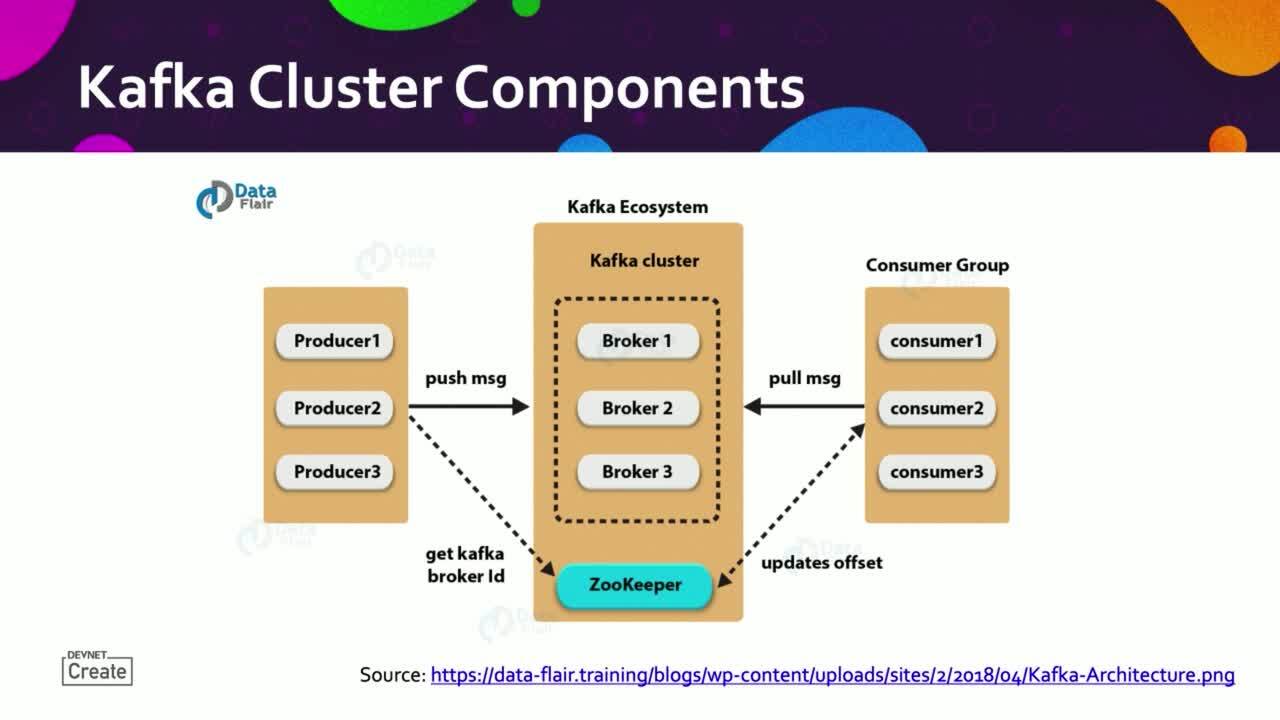
Kafka real-time data streaming for Network Engineers
Apache Kafka is an open-source framework implementation of a high-throughput, low-latency data streaming service. Originally developed by LinkedIn, it is now open-sourced and used by large and small companies worldwide.
19:41
-
Cisco Innovation Labs Tour
Cisco Innovation Labs Tour
6:40
-
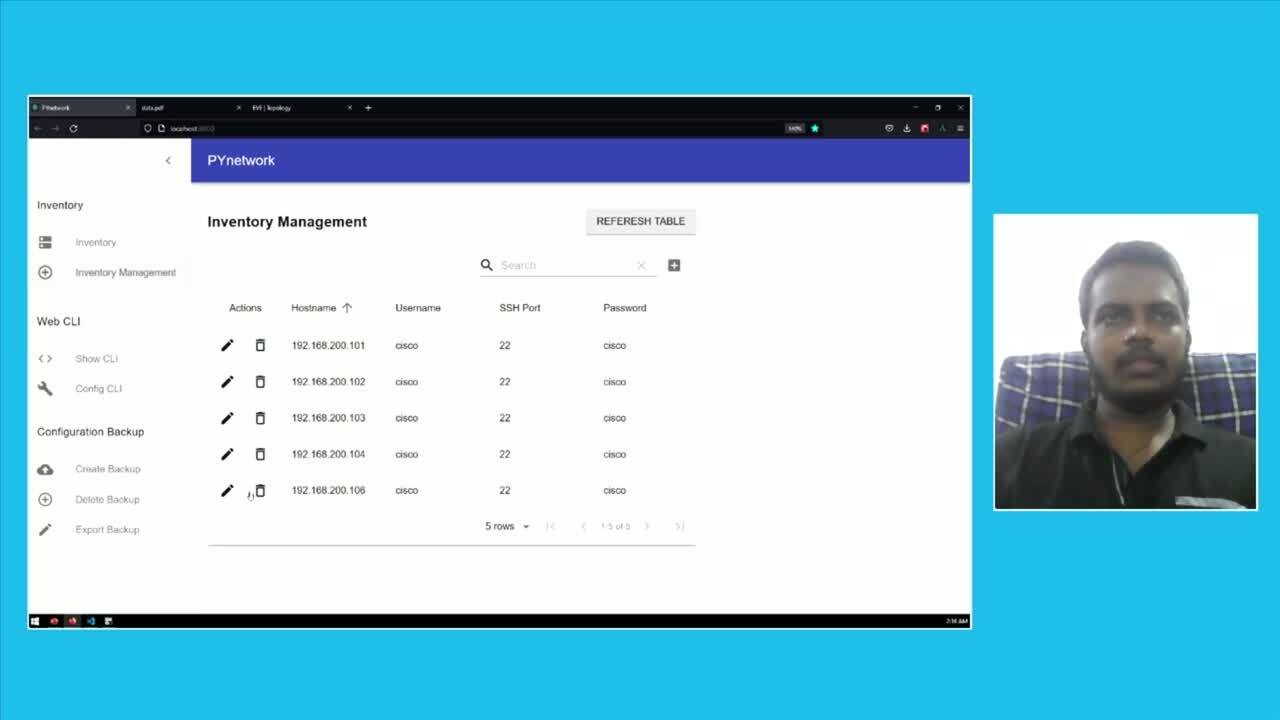
Automate the Network with WEB GUI PYnetwork
It is a Web based Network Automation tool, Backend - flask, front-end React and Material UI and database is sqlite.
9:37
-
Watch how streaming telemetry, open-source tooling, and APIs turn into an amazing BBQ setup. DevNet Snack Minute Episode 42.
Join Matt and Kareem as they chat with Developer Advocate Quinn Snyder, as he demonstrates using streaming telemetry concepts and open-source tooling, along with some handy APIs, to achieve perfect data-driven outcomes and delicious meal results.
16:46
-
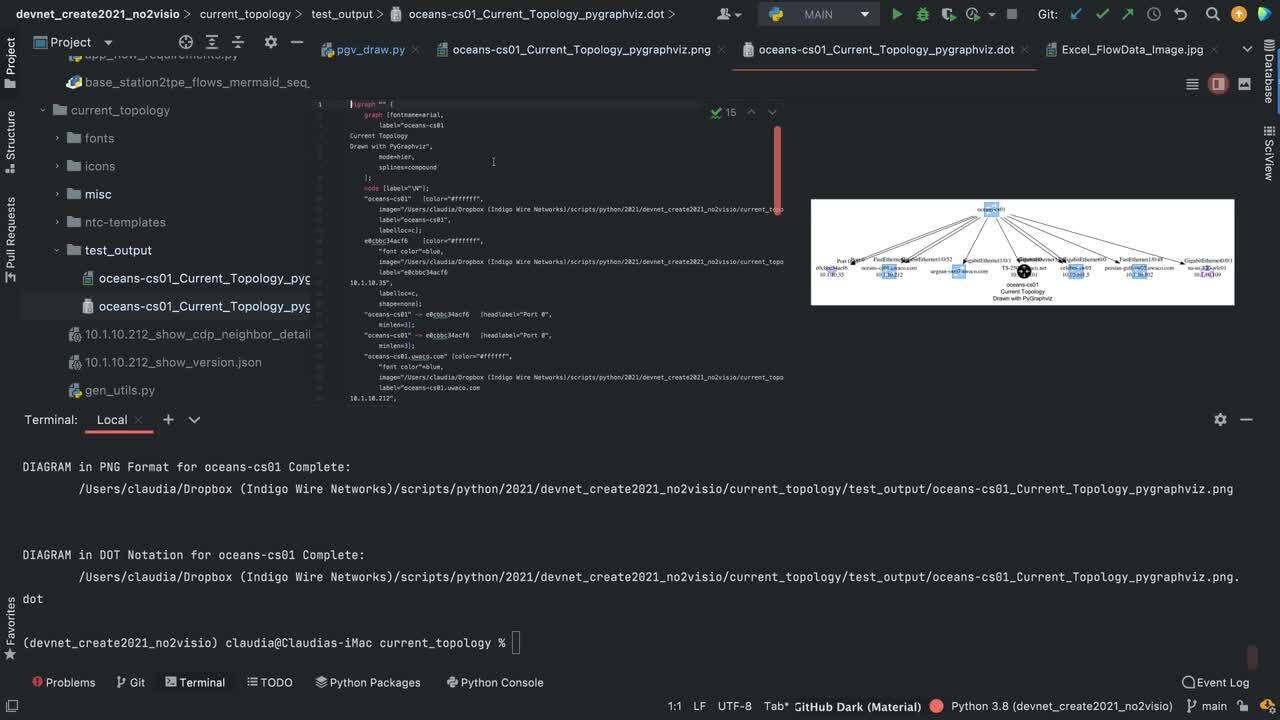
Just say no to Visio
From design documentation to as-builts a good network engineer spends a substantial amount of time drawing. It is time to explore "Documentation as Code" and it make sense to start with diagrams.
18:51
-
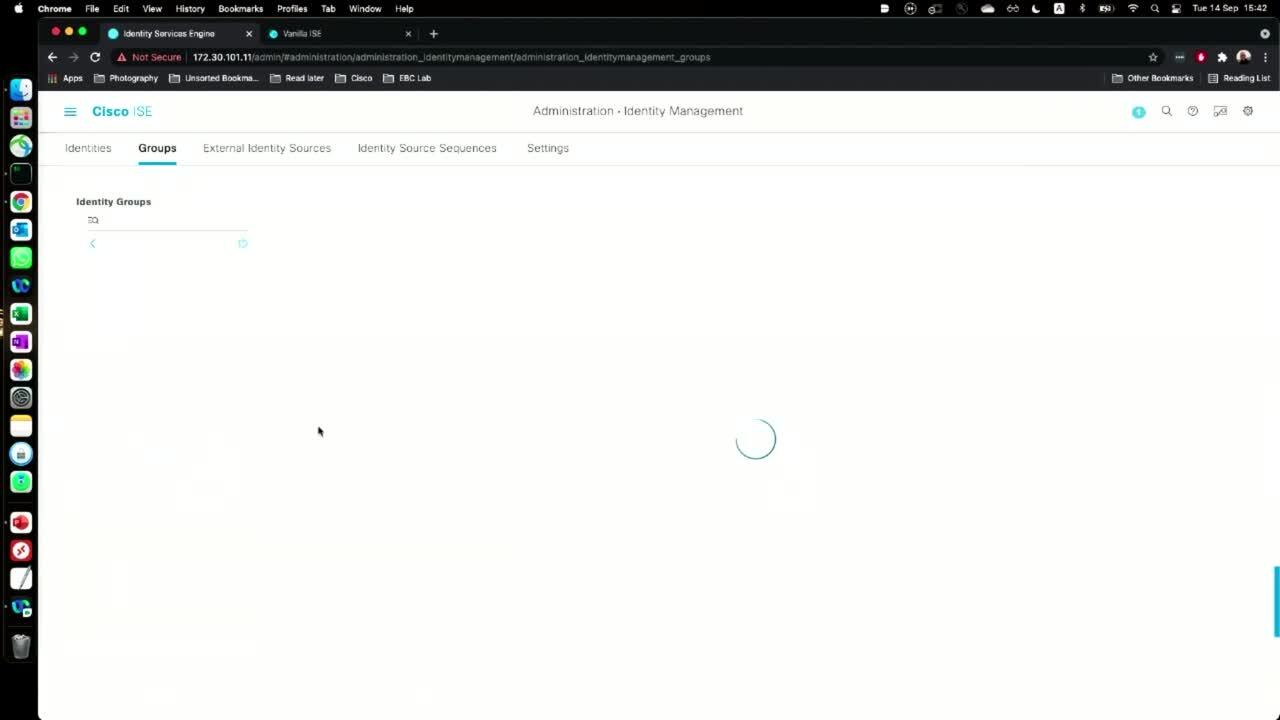
Making ice cream with Vanilla ISE
Vanilla ISE is a simplified UI for Cisco ISE, leveraging ISE's open APIs.
20:10
-
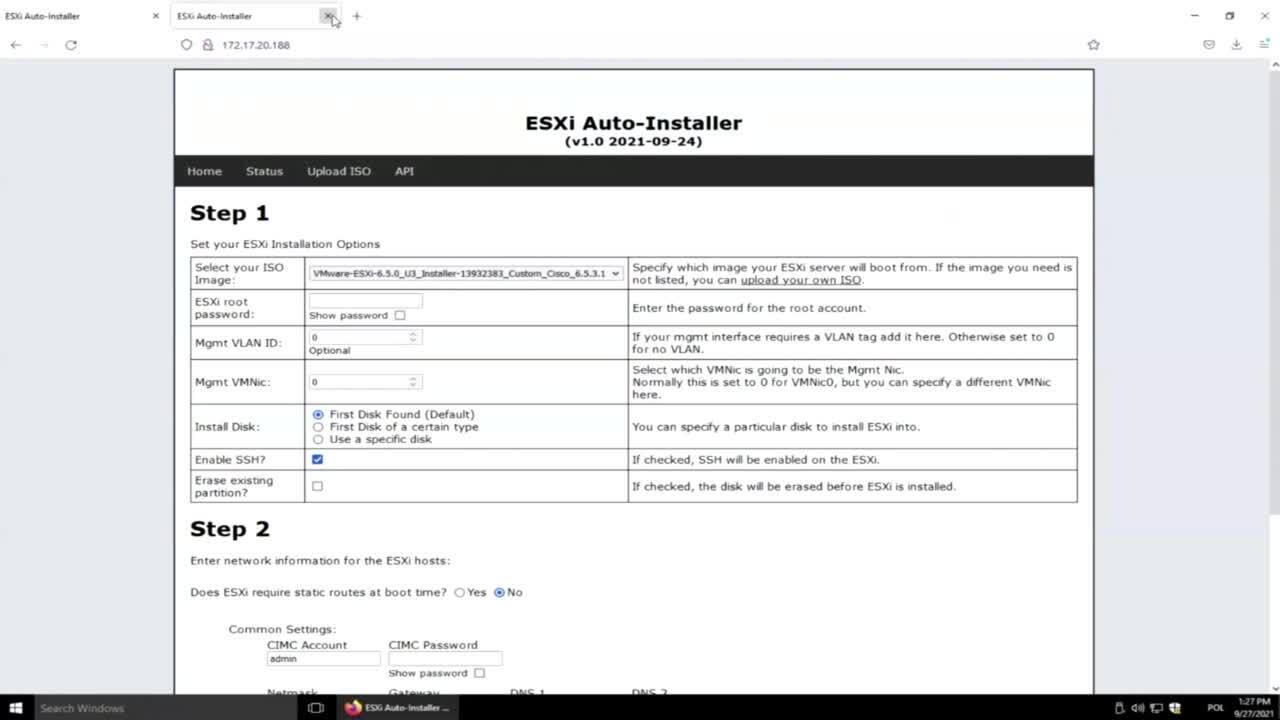
Automated ESXi Installs
Ever installed ESXi so many times that yellow console screen is burned into your eyes? Using basic DevNet concepts like Python, a Web Page, and APIs, this code enables mass ESXi deployments on Cisco Platforms without logging into an ESXi console.
8:17
-
Secure CN - Securing Cloud Native Applications
Cloud-native application security involves balancing the benefits of cloud services in accelerating development while at the same time handling security in an adverse environment with more attack surfaces and opportunities for data breaches.
20:09
-
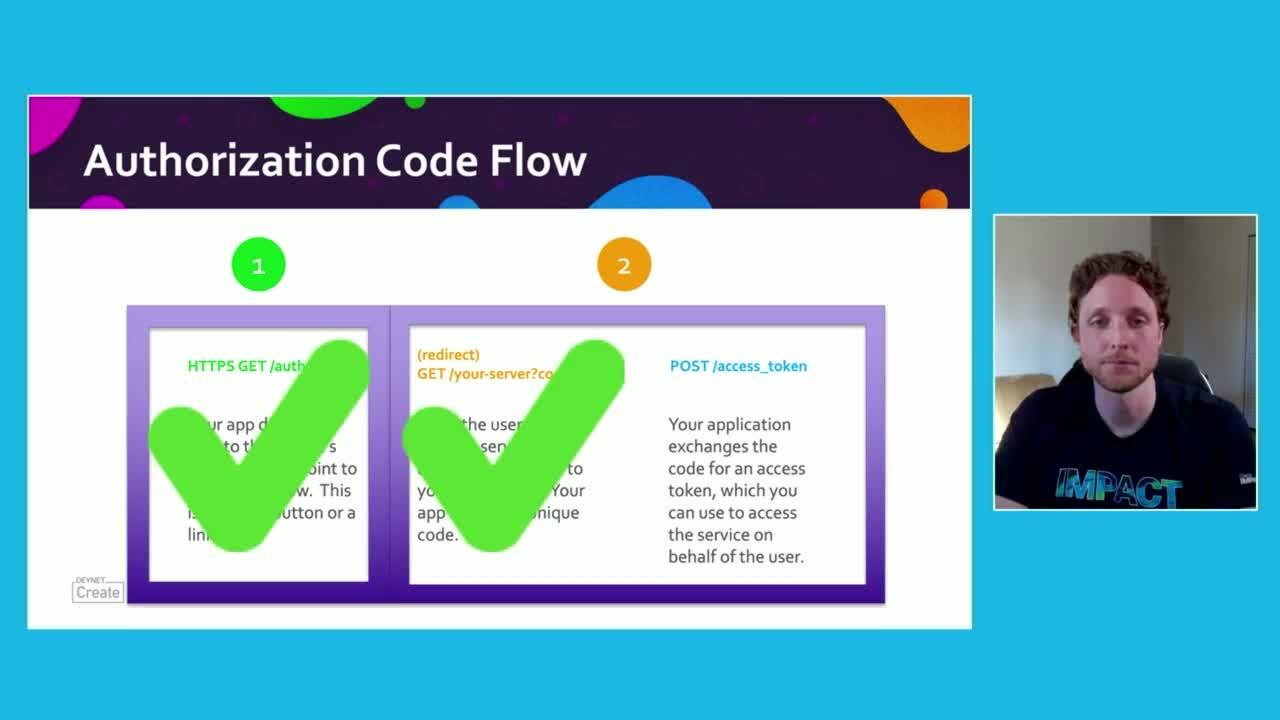
How to use OAuth Authorization Code Flow
How to use OAuth Authorization Code Flow
15:06
-
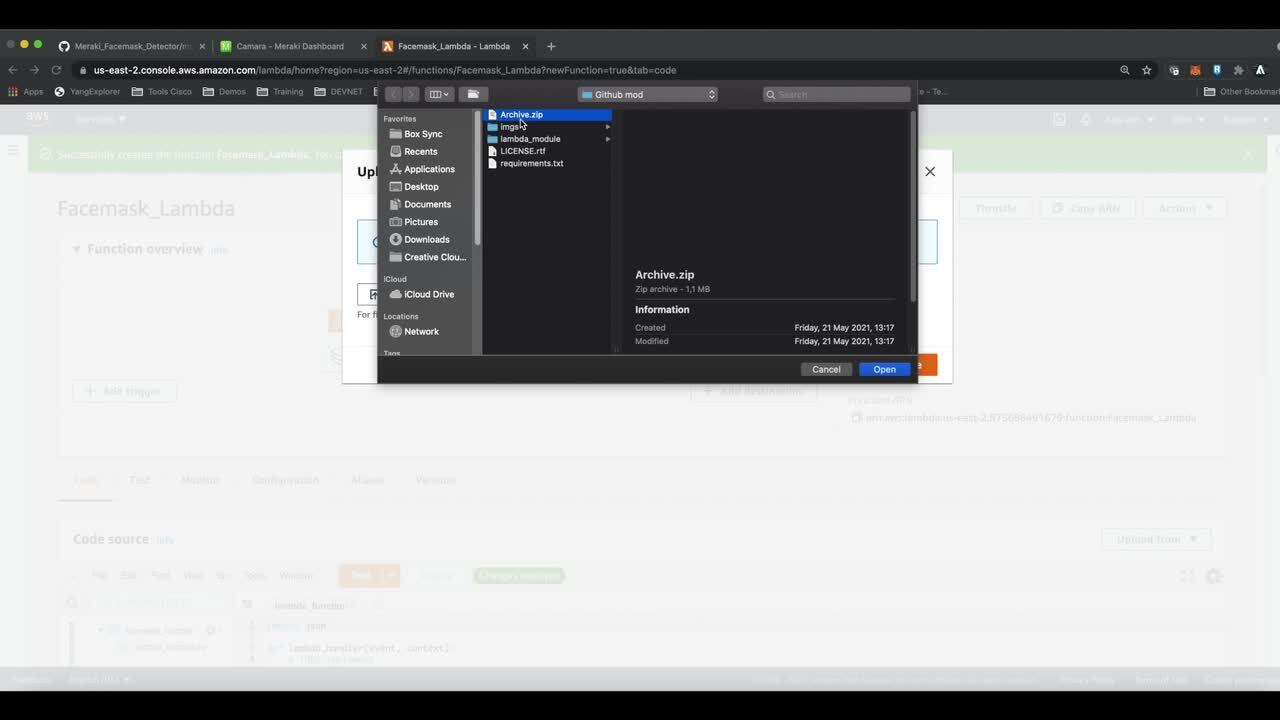
Meraki MV APIs + AWS Rekognition = Powerful image analytics!
Meraki MV Cameras are great, but what if we need to extend their visual intelligence even more? In this session, we will show you how you can get a deep image analysis through the integration between Meraki MV Sense APIs and Amazon AWS Rekognition.
9:09
-
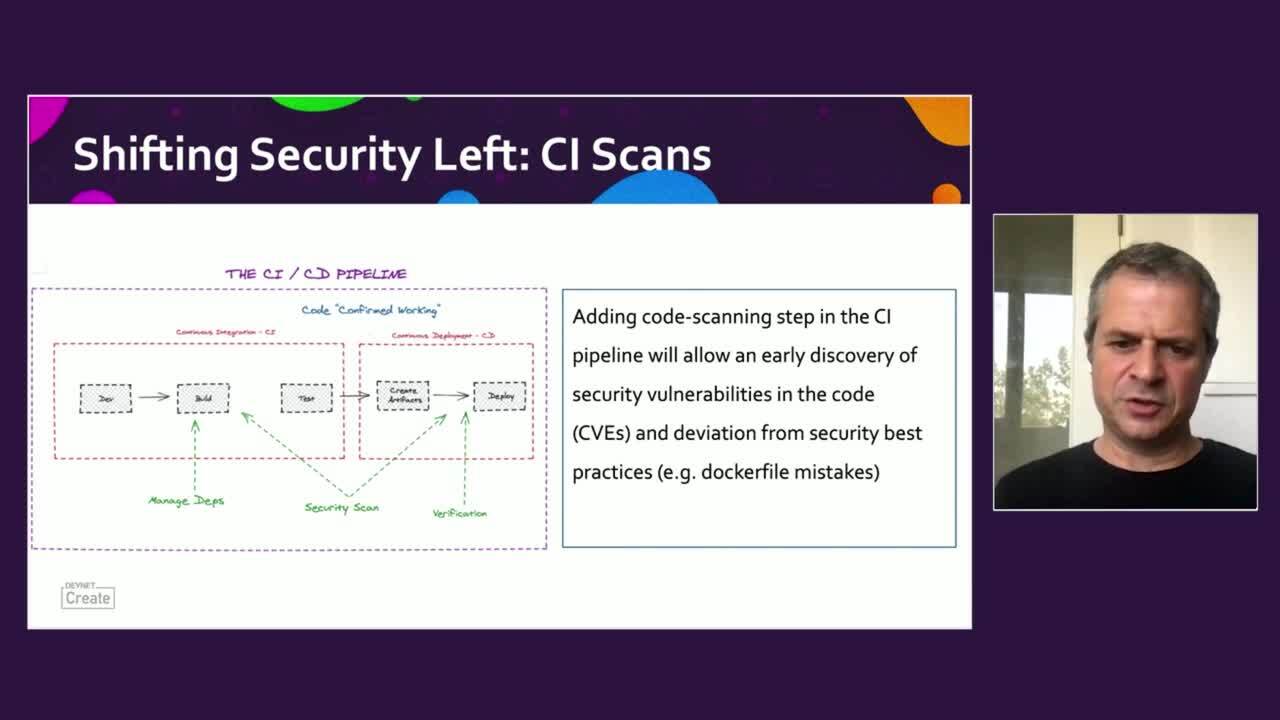
Shift Left Security: How Developers can Assume Responsibility on their Apps
Cloud applications/microservices architecture require a shift left in responsibilities, both deployments and security aspects.
18:44
- Load More
Cisco Video Portal


Share this video
Embed
Size: x pixels