Use of FQDN Object in Access Policy Firepower Threat Defense
3:27
This video demonstrates the use of FQDN object in access policy on Firepower Threat Defense Tags: Security Firepower
Related Videos
In Technical Assistance Center (TAC)
-
Play video Configure SPAN capture and apply traffic filters
Configure SPAN capture and apply traffic filters
This video describes the process to configure SPAN capture and apply ACL to filter specific traffic
2:39
-
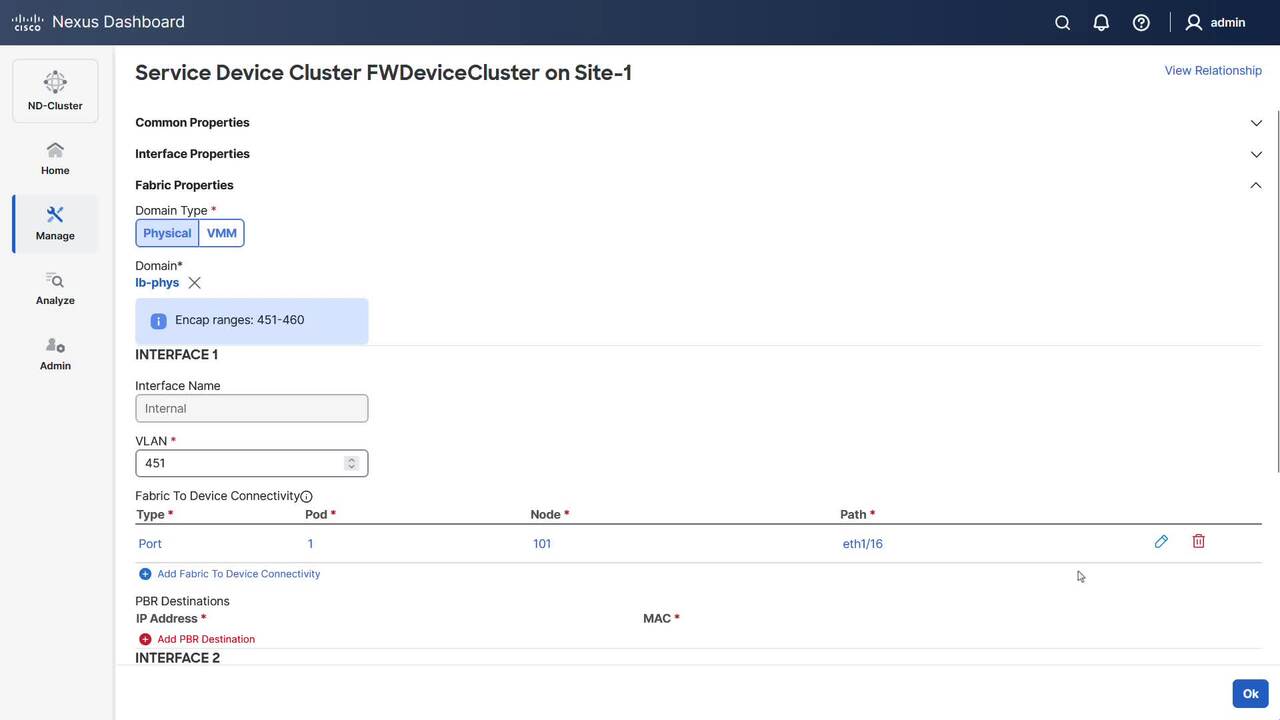
Play video Configure Service Chaining for E-W Traffic in NDO
Configure Service Chaining for E-W Traffic in NDO
This video demonstrates how to configure service chaining in NDO for EPG-to-EPG communication in single site.
6:25
-
Play video Collect CUAC Advanced Server Logs
Collect CUAC Advanced Server Logs
This video describe the proces to collect CUAC Advaned Server logs. Tags:cuac,logs
1:27
-
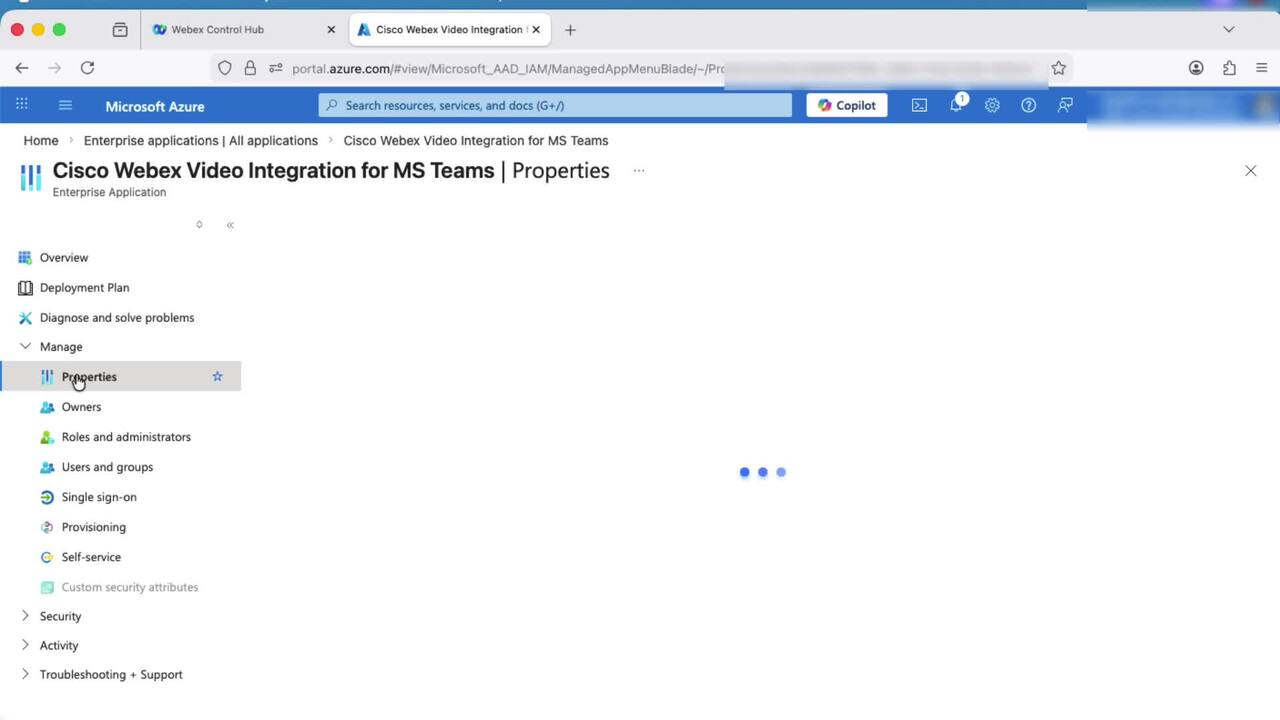
Play video How to Resolve "Impaired Service" error for VIMT on Webex Control Hub
How to Resolve "Impaired Service" error for VIMT on Webex Control Hub
This video provides steps on how to resolve the "Impaired Service" error for VIMT (Video Integration for Microsoft Teams) on Control Hub.
2:52
-
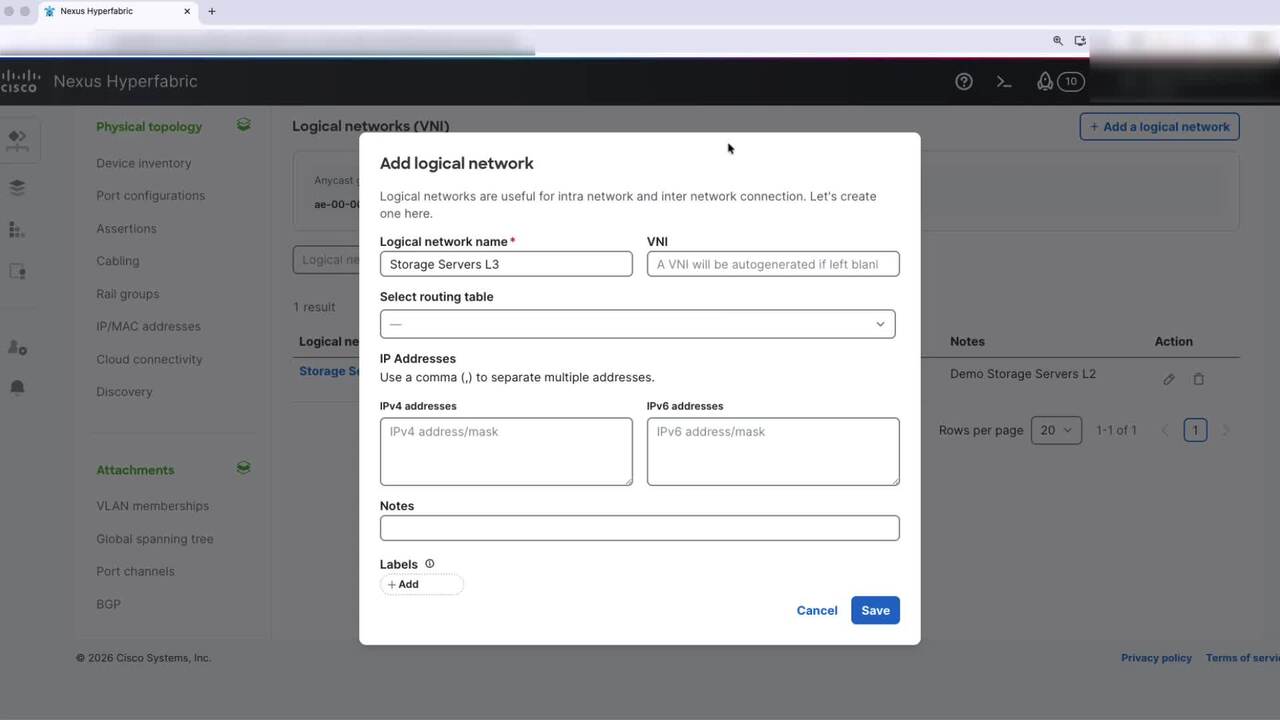
Play video Hyperfabric - Add Logical Network (VNI)
Hyperfabric - Add Logical Network (VNI)
This video will walk you through the process of creating a logical network in Cisco Hyperfabric. You can create either a Layer 2 or Layer 3 logical network, depending on your segmentation and routing needs.
2:26
-
Play video SPAN to CPU in Cisco ACI
SPAN to CPU in Cisco ACI
This video describes how to configure and use ACI SPAN to CPU feature for troubleshooting.
4:41