Cisco Cyber Vision Overview
21:02
This video offers a detailed overview of the Cyber Vision architecture and demonstrates most of its features.
Related Videos
In Security
-
Play video The AI Ready Enterprise: Building a Secure Network Architecture for What's Next
The AI Ready Enterprise: Building a Secure Network Architecture for What's Next
Campus networks are under pressure— increased traffic, AI workloads, hybrid work, and a rising tide of IoT devices create unprecedented risks. Simplify and secure your AI-ready infrastructure with scalable, integrated security solutions to deliver a
2:22
-
Play video Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Discover the key cyberthreats targeting service providers, from espionage-driven advanced persistent threats (APTs) to silent intrusions and tough infrastructure decisions, and the risks they pose to critical networks.
2:36
-
Play video AI-Ready Wireless Security: Integrating WPA3 & Beyond
AI-Ready Wireless Security: Integrating WPA3 & Beyond
Delve into AI-Ready Wireless Security: WPA3's evolution from WEP, its role in Wi-Fi 6E/7 (MLO, EHT), and enhanced cryptography. Covers holistic network security & emerging post-quantum cryptography to counter future threats.
18:53
-
Play video Cisco Cyber Vision: Protecting OT at Scale
Cisco Cyber Vision: Protecting OT at Scale
Get unparalleled visibility and threat detection across operational technology networks by analyzing industrial protocols and integrating with Cisco security products to secure OT environments at scale.
1:56
-
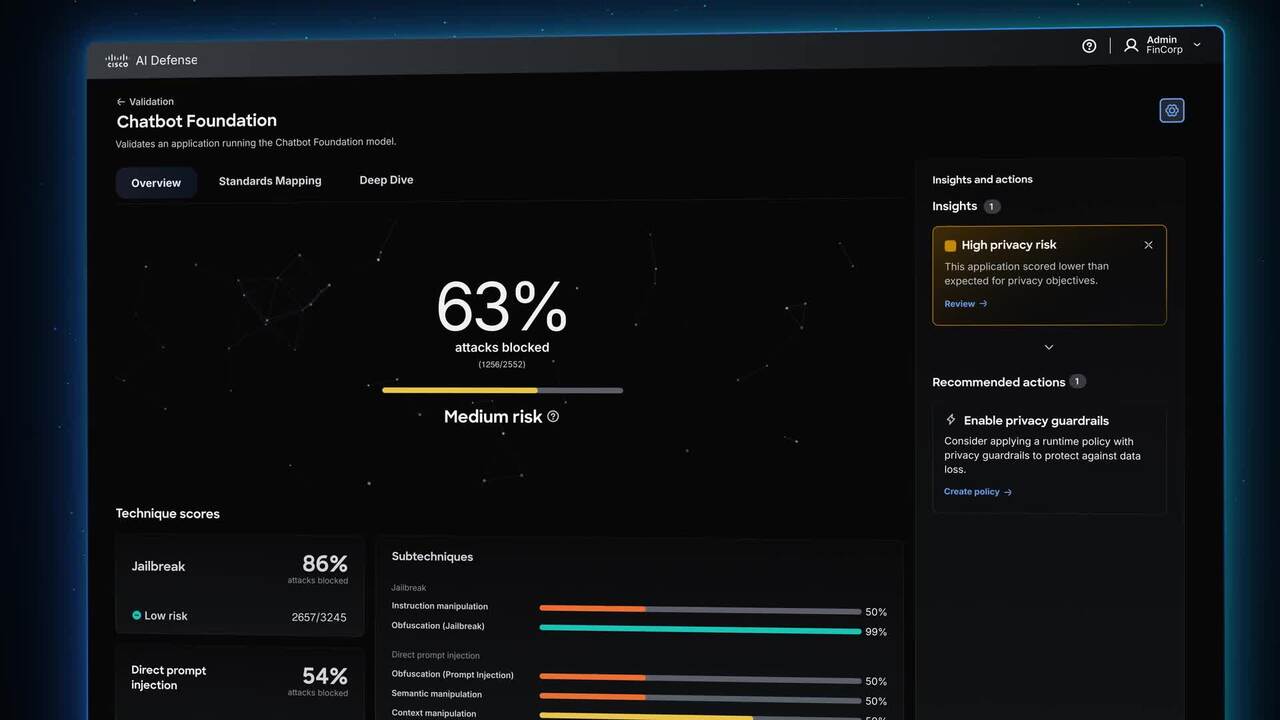
Play video Meet Cisco AI Defense
Meet Cisco AI Defense
Security built for the AI era. What stands between you and AI's promise is the unknown-new attack vectors, hidden AI assets, and risks traditional security can't see. Cisco AI Defense secures the AI lifecycle so teams can innovate with confidence.
2:19
-
Play video Cisco Secure Firewall 6100 Series - Highest performance density for AI-ready data centers
Cisco Secure Firewall 6100 Series - Highest performance density for AI-ready data centers
The Cisco Secure Firewall 6100 Series is an ultra-high-end series firewall that protects AI-ready data centers and telecom mobility infrastructure with exceptional performance density, line-rate advanced threat protection, and modular scalability.
1:37