Quantum hurdles: an optimistic view of post-quantum security
35:43
Sander Dorigo (Fox Crypto) - Presentation from SECCON NL 2022
Related Videos
In Security
-
Play video Meet Cisco AI Defense
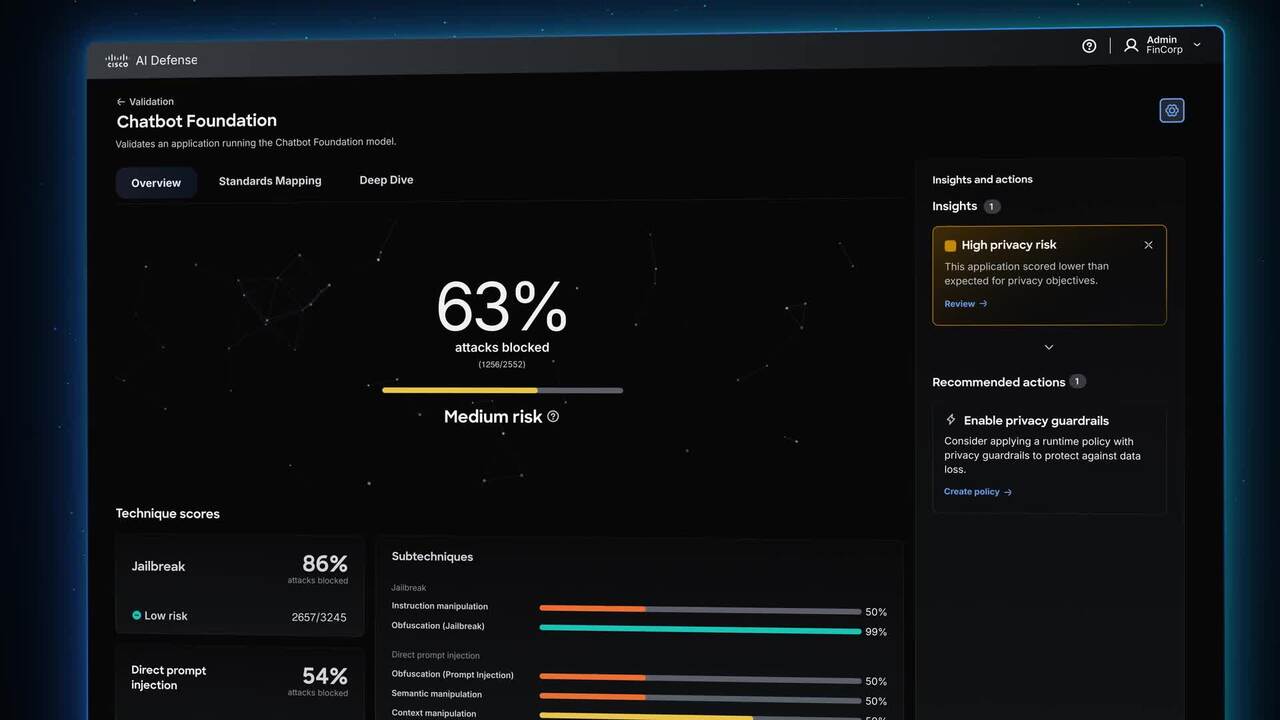
Meet Cisco AI Defense
Security built for the AI era. What stands between you and AI's promise is the unknown-new attack vectors, hidden AI assets, and risks traditional security can't see. Cisco AI Defense secures the AI lifecycle so teams can innovate with confidence.
2:19
-
Play video Secure Campus Overview Video
Secure Campus Overview Video
As AI is embedded into daily workflows, campus networks must be simpler to operate, secure by design, and built for real-time performance. Cisco Secure Campus achieves this with Agentic Operations, integrated security, and high-performance networking
2:15
-
Play video SASE for the AI Era from Cisco
SASE for the AI Era from Cisco
Your organization can do amazing things with AI, if your network is ready for it. Cisco's SASE solution is designed to meet the new needs of the AI era - by identifying, optimizing, and securing AI traffic flows.
1:46
-
Play video Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Discover the key cyberthreats targeting service providers, from espionage-driven advanced persistent threats (APTs) to silent intrusions and tough infrastructure decisions, and the risks they pose to critical networks.
2:36
-
Play video The Power of the Platform: Cisco SASE
The Power of the Platform: Cisco SASE
By integrating market-leading SD-WAN with cloud-native SSE, Cisco SASE delivers secure access in an optimized and orchestrated way. See each component working together - identifying and optimizing the best - and most secure - path for your business.
2:03
-
Play video How Cisco’s Cutting-Edge Tech Keeps 70,000 49ers Fans Safe & Connected
How Cisco’s Cutting-Edge Tech Keeps 70,000 49ers Fans Safe & Connected
49ers EVP Costa Kladianos explains why he trusts Cisco to power the team’s biggest NFL moments, including Super Bowl LX.
0:33