Secure Email Threat Defense Demo
2:20
An overview of the innovative and differentiating features within Secure Email Threat Defense. Take a detailed look at the unprecedented level of detail about the intent and risk an email-based threat poses to an organization.
Related Videos
In Security
-
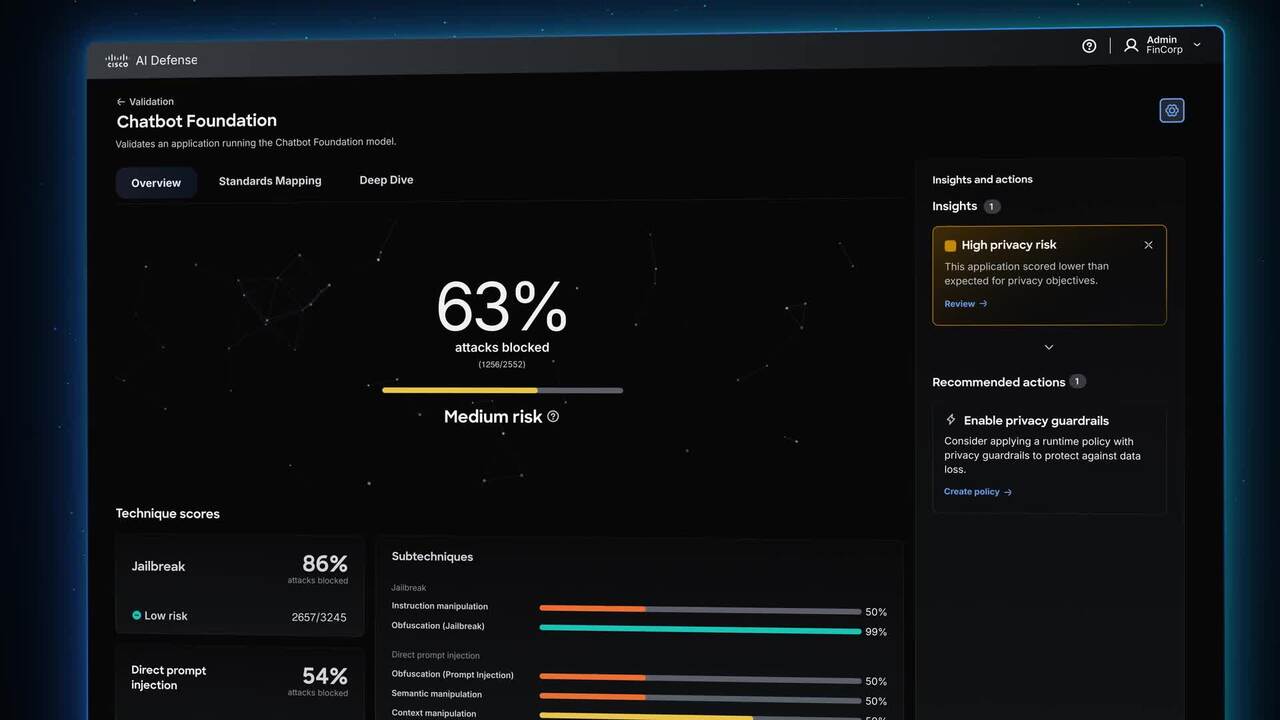
Play video Meet Cisco AI Defense
Meet Cisco AI Defense
Security built for the AI era. What stands between you and AI's promise is the unknown-new attack vectors, hidden AI assets, and risks traditional security can't see. Cisco AI Defense secures the AI lifecycle so teams can innovate with confidence.
2:19
-
Play video AI-Ready Wireless Security: Integrating WPA3 & Beyond
AI-Ready Wireless Security: Integrating WPA3 & Beyond
Delve into AI-Ready Wireless Security: WPA3's evolution from WEP, its role in Wi-Fi 6E/7 (MLO, EHT), and enhanced cryptography. Covers holistic network security & emerging post-quantum cryptography to counter future threats.
18:53
-
Play video Cisco Cyber Vision: Protecting OT at Scale
Cisco Cyber Vision: Protecting OT at Scale
Get unparalleled visibility and threat detection across operational technology networks by analyzing industrial protocols and integrating with Cisco security products to secure OT environments at scale.
1:56
-
Play video Secure Campus Overview Video
Secure Campus Overview Video
As AI is embedded into daily workflows, campus networks must be simpler to operate, secure by design, and built for real-time performance. Cisco Secure Campus achieves this with Agentic Operations, integrated security, and high-performance networking
2:15
-
Play video SASE for the AI Era from Cisco
SASE for the AI Era from Cisco
Your organization can do amazing things with AI, if your network is ready for it. Cisco's SASE solution is designed to meet the new needs of the AI era - by identifying, optimizing, and securing AI traffic flows.
1:46
-
Play video Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Footholds in Infrastructure: Defending Service Providers from Cyberthreats
Discover the key cyberthreats targeting service providers, from espionage-driven advanced persistent threats (APTs) to silent intrusions and tough infrastructure decisions, and the risks they pose to critical networks.
2:36