AI RRM Boost Wireless Performance
1:10
Watch this short demo to see how AI RRM drives more reliable wireless performance, automates radio frequency management, and minimizes interference!
Related Videos
In Latest Videos
-
Play video Interview with TD Synnex about Cisco Secure AI Factory with NVIDIA
Interview with TD Synnex about Cisco Secure AI Factory with NVIDIA
Cisco’s Cassie Roach and Loïc d'Ursel of TD Synnex discuss why TD Synnex is making an investment in the Cisco Secure AI Factory with NVIDIA.
4:10
-
Play video Upgrade NSO Network Element Driver (NED)
Upgrade NSO Network Element Driver (NED)
This video demonstrates the process of upgrading NSO Network Element Drivers (NEDs) to a newer version. It covers both: backward compatible upgrades and non-backward compatible migrations. Tags: NSO, NED, upgrade, migration
7:13
-
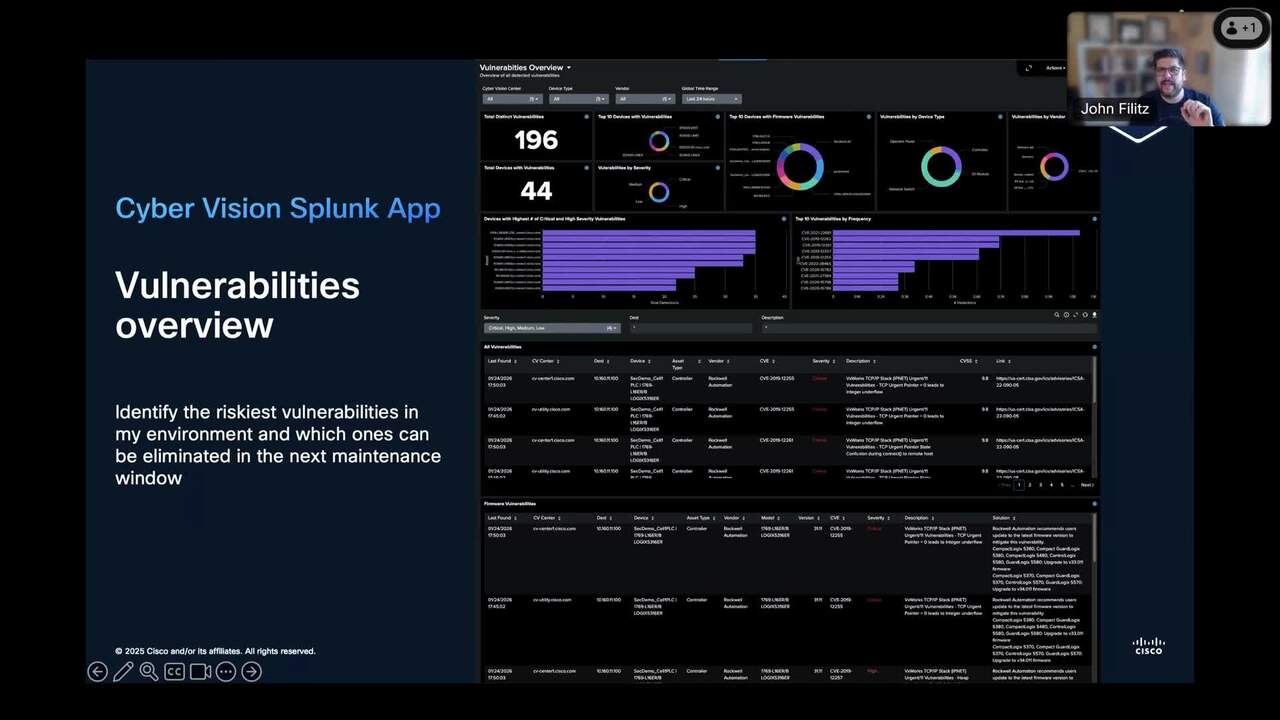
Play video Managing Multi-Site OT Security with Cyber Vision and Splunk
Managing Multi-Site OT Security with Cyber Vision and Splunk
Learn how we're enhancing Cyber Vision to drive OT visibility and security in large, multi-site customer deployments. This session showcases new multi-site management capabilities, and highlights how Splunk can help visualize OT security data.
24:02
-
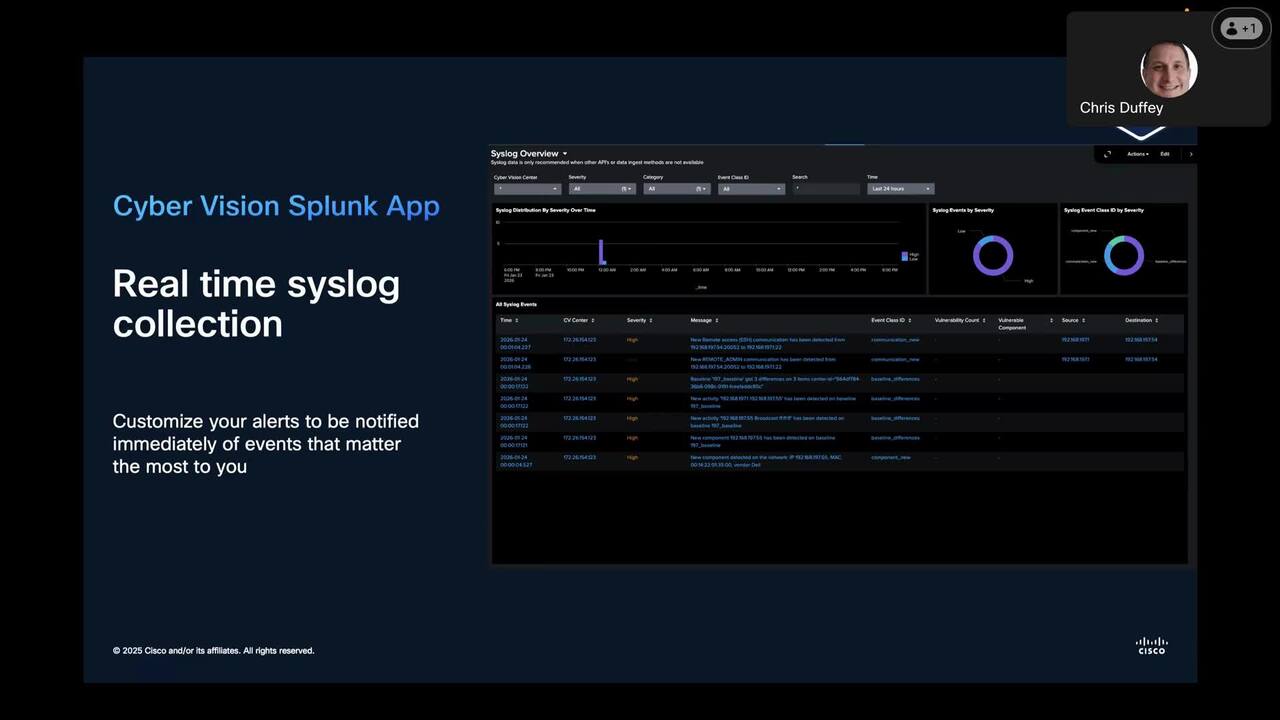
Play video Securing industrial networks with Cisco and Splunk
Securing industrial networks with Cisco and Splunk
Protect the global enterprise with a solution that gives you visibility over both your IT and OT domains and the entire attack chain. Learn how Splunk uses Cisco Cyber Vision to detect and investigate threats across the entire digital landscape.
22:24
-
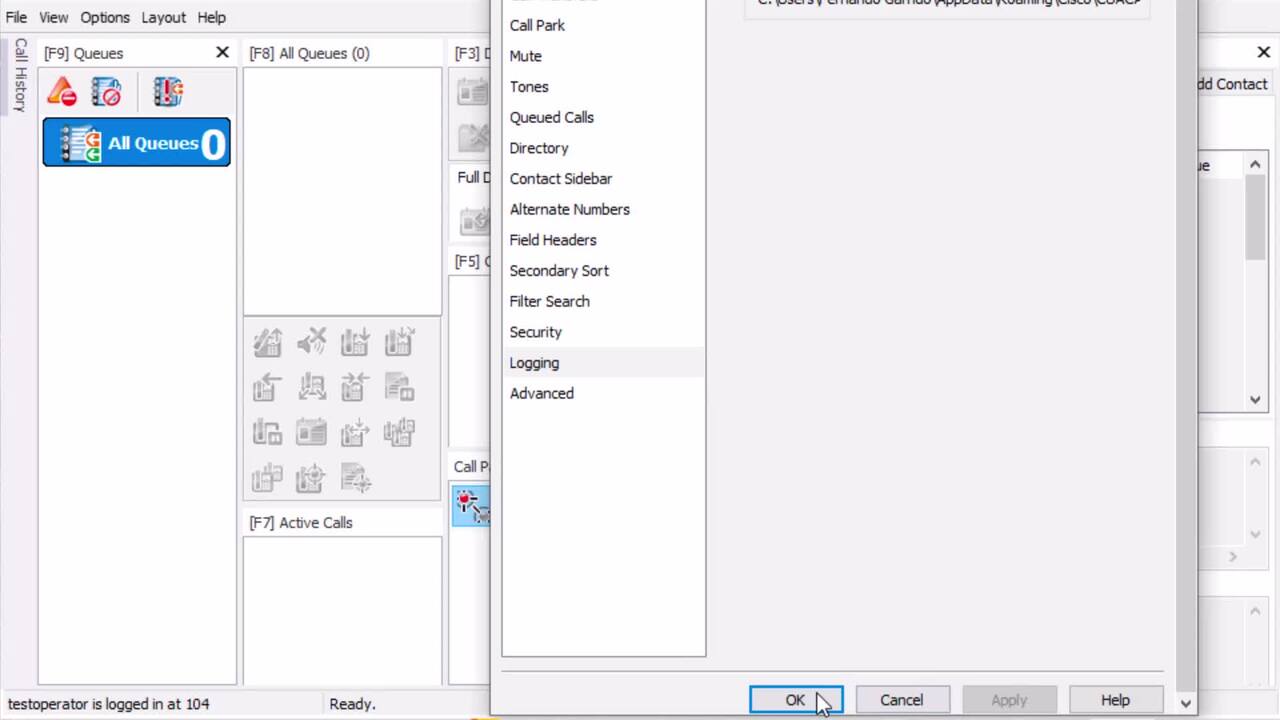
Play video Collect CUAC Advanced Client Logs
Collect CUAC Advanced Client Logs
This video describe the proces to collect CUAC Advanced Client logs.
1:13
-
Play video How to manage Network Admission Control like BBVA / How I Cisco
How to manage Network Admission Control like BBVA / How I Cisco
Learn how BBVA manages Network Admission Control (NAC) at scale using Cisco Software Defined Access (SDA) and Cisco SDWAN. See how the bank modernized network access by implementing secure user mobility, and automation.
1:13