Transitioning to Secure Client from SecureX
6:31
This brief demo explains how Secure Client transitions into a stand-alone application that will transfer existing orgs and data from SecureX at the End of Life of SecureX on July 31, 2024.
Related Videos
In Latest Videos
-
Play video How Digital Realty Is Accelerating ROI by Reimagining AI Deployment
How Digital Realty Is Accelerating ROI by Reimagining AI Deployment
Discover how Digital Realty—a leader in data center solutions—designed an innovative approach to AI deployment, empowering customers to see results faster. CTO Chris Sharp shares more and discusses how Cisco tech helped make it happen.
3:39
-
Play video Digital Resilience in the AI Era: IDC on Unified Operational Visibility
Digital Resilience in the AI Era: IDC on Unified Operational Visibility
AI is fragmenting operational data across the stack. IDC explains why digital resilience is a data problem—and what it takes to unify signals for real-time visibility and faster action.
0:39
-
Play video Simple, Secure & Unified from Core to Edge: Cisco Secure AI Factory with NVIDIA
Simple, Secure & Unified from Core to Edge: Cisco Secure AI Factory with NVIDIA
Scaling AI shouldn't mean added complexity. Cisco Secure AI Factory with NVIDIA delivers a unified, secure operating model—from core to edge. Validated designs, built-in security, and Splunk end-to-end observability from AI agents to infrastructure.
1:52
-
Play video How to Configure FED CPU Capture on C9k Switches
How to Configure FED CPU Capture on C9k Switches
Tutorial on how to configure and use FED CPU Punt and Inject capture on Catalyst 9000 series switches. Tags:C9000,C9k,Catalyst9k,packet loss,drops,packet capture,broadcast storm
4:16
-
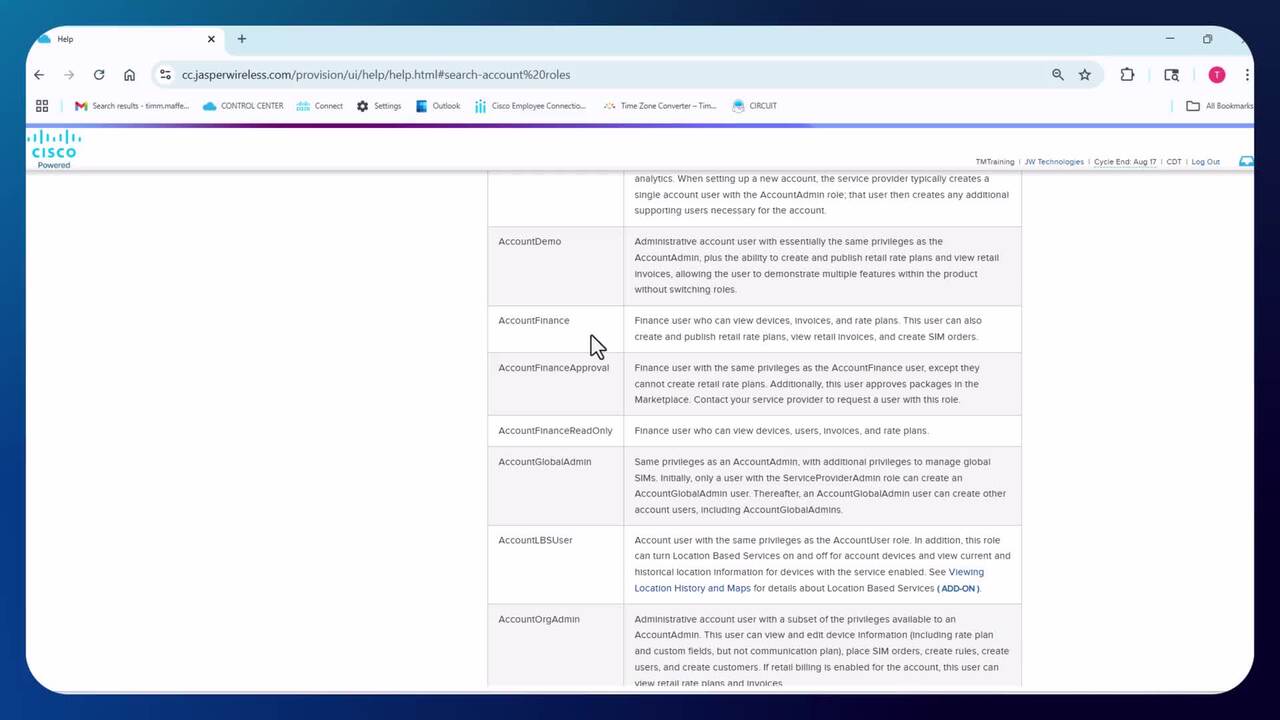
Play video Admin Page
Admin Page
Understand the basic features of the Control Center Admin Page
6:04
-
Play video Securing AI from Core to Edge: Cisco Secure AI Factory with NVIDIA
Securing AI from Core to Edge: Cisco Secure AI Factory with NVIDIA
AI expands the attack surface. Cisco Secure AI Factory with NVIDIA fights back. Security engineered into every layer—models, apps, AI workloads, and infrastructure. From core to edge, trusted AI starts here.
1:41