Quantum hurdles: an optimistic view of post-quantum security
35:43
Sander Dorigo (Fox Crypto) - Presentation from SECCON NL 2022
Related Videos
In Latest Videos
-
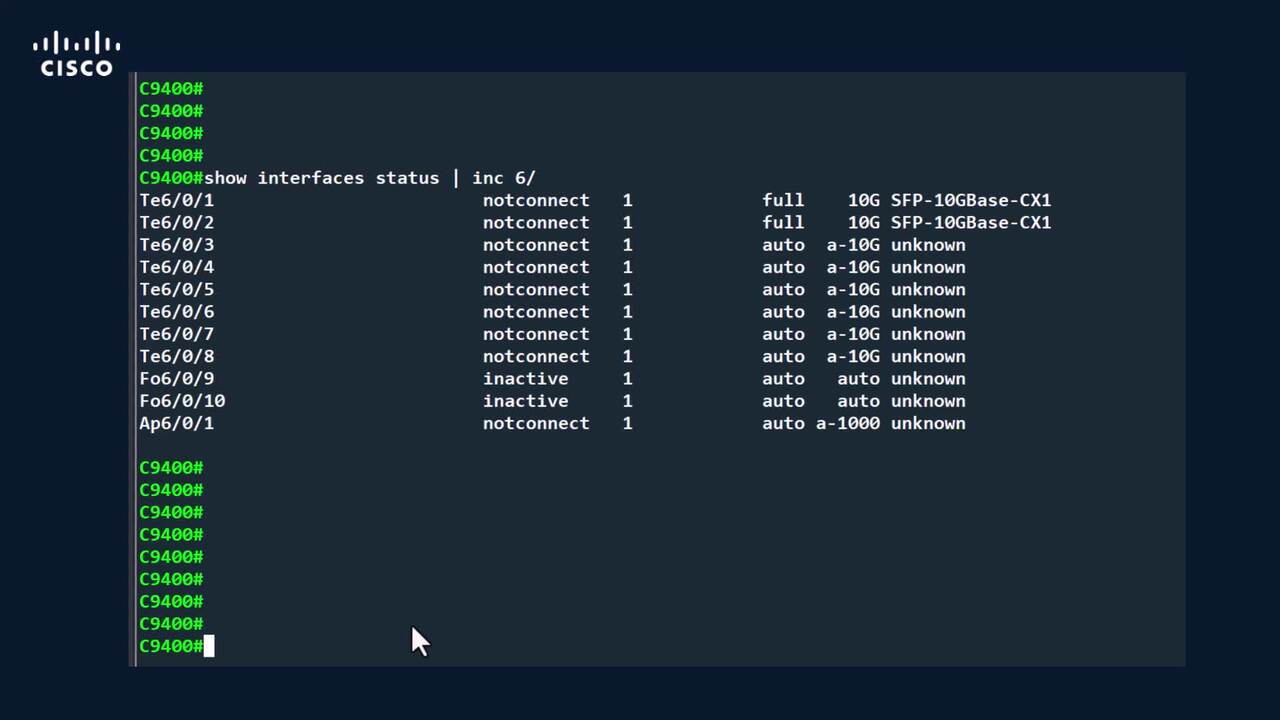
Play video Uplink port configurations for C9400 standalone SUP1 models
Uplink port configurations for C9400 standalone SUP1 models
This video demosntatres the uplink ports configurations available on C9400 SUP-1 modules Tags: Cat9400,SUP-1
5:36
-
Play video Configure and Verify Syslog on UCS Intersight Managed Mode
Configure and Verify Syslog on UCS Intersight Managed Mode
In this video, we explain how to Configure and Verify Syslog on UCS Intersight Managed Mode.
3:45
-
Play video From Mobility to Physical AI: Ava powers connected intelligence for next-gen networks
From Mobility to Physical AI: Ava powers connected intelligence for next-gen networks
Cisco Mobility evolves beyond connectivity into AI-powered networks. With the Mobility Services Platform, Ava delivers real-time insights and automation—enabling smarter operations, predictive intelligence, and scalable transformation.
2:36
-
Play video How to Upgrade Nexus 9000 Switches Using NDFC
How to Upgrade Nexus 9000 Switches Using NDFC
This video provide step by step guide to upgrade Nexus Switches 9000 NXOS Software via NDFC Tags: dcnexus
2:41
-
Play video Lessons from the agentic frontier: How the SOC is winning in the AI era | RSAC 2026 Splunk Keynote
Lessons from the agentic frontier: How the SOC is winning in the AI era | RSAC 2026 Splunk Keynote
John Morgan, SVP and GM of Security at Splunk, and Fred Frey, Director of Al Engineering for Security at Splunk shared practical insights on building a human-led, machine-accelerated Security Operations Center (SOC).
22:14
-
Play video AI for Retail: Boost Sales with Predictive Data Analytics | Tech Unscripted
AI for Retail: Boost Sales with Predictive Data Analytics | Tech Unscripted
In Tech Unscripted, Cisco's Brian Jones and Samsoe Samsoe's Simon Solarsky explore bridging online and in-store retail. See how predictive analytics and Wi-Fi 7 turn IT from a cost center into a powerful engine for business growth.
23:29