Use of FQDN Object in Access Policy Firepower Threat Defense
3:27
This video demonstrates the use of FQDN object in access policy on Firepower Threat Defense Tags: Security Firepower
Related Videos
In Government
-
Play video Digital Resilience in the AI Era: IDC on Unified Operational Visibility
Digital Resilience in the AI Era: IDC on Unified Operational Visibility
AI is fragmenting operational data across the stack. IDC explains why digital resilience is a data problem—and what it takes to unify signals for real-time visibility and faster action.
0:39
-
Play video Beutlhauser’s Network Transformation: Achieving Simplicity and Speed with Cisco
Beutlhauser’s Network Transformation: Achieving Simplicity and Speed with Cisco
Learn how Beutlhauser leverages Cisco networking solutions to gain complete network visibility and control. With a single dashboard for all locations, the team now deploys new sites in hours, ensuring a fast, efficient, and scalable network backbone
2:20
-
Play video E80 is Transforming Factory Automation
E80 is Transforming Factory Automation
Learn how E80 is helping manufacturers secure their plant floors with autonomous vehicles that embed secure industrial networking, from Cisco IE switches to Cyber Vision, ISE, and Cisco URWB.
2:22
-
Play video How the US Open Delivers 4x Faster Wireless with Wi-Fi 7
How the US Open Delivers 4x Faster Wireless with Wi-Fi 7
Experience seamless digital ticketing and lower latency at the U.S. Open with Cisco Wi-Fi 7 wireless. Cisco Wi-Fi 7 handles high-density congestion for 40,000+ fans while delivering 4x faster speeds.
1:06
-
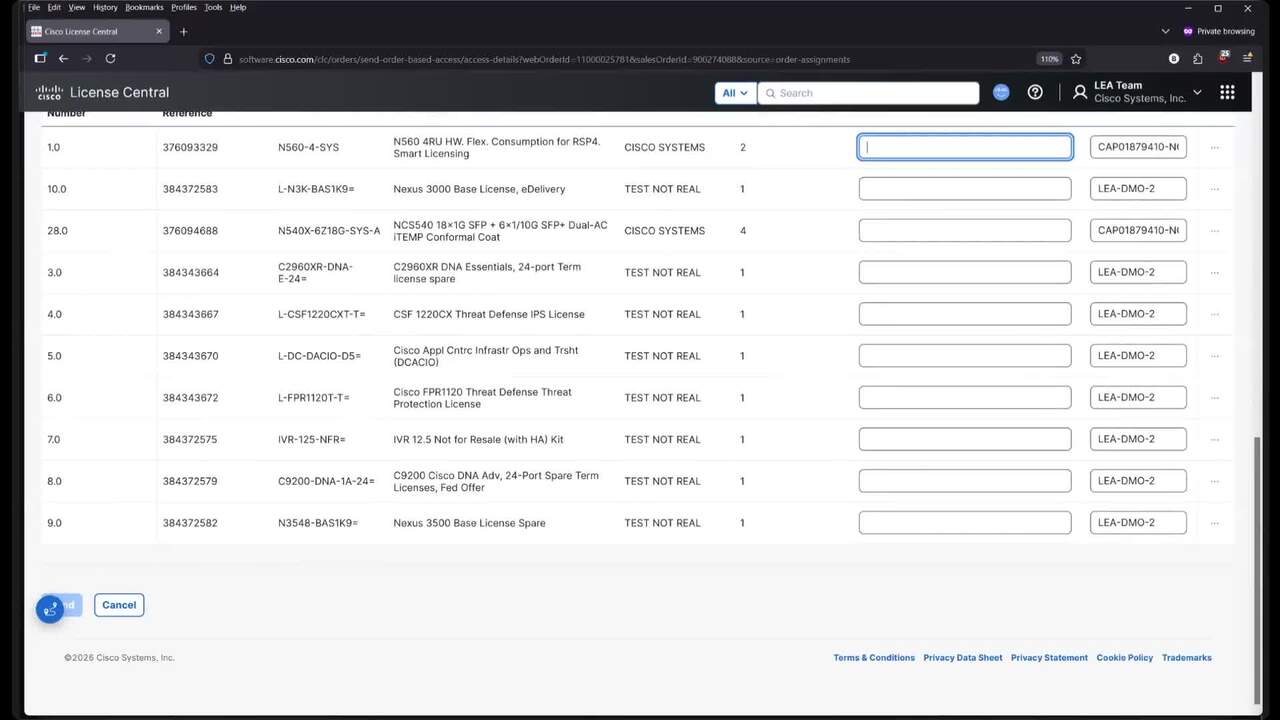
Play video Cisco License Central: Smart Account Creation, SA Assignment in Orders tab, provisioning pending orders
Cisco License Central: Smart Account Creation, SA Assignment in Orders tab, provisioning pending orders
Discover Smart Account Administration capabilities integrated within Cisco License Central. We'll walk through Smart Account creation, Smart account assignment to orders & more.
44:13
-
Play video Configure Disjoint Layer 2 in IMM Domain
Configure Disjoint Layer 2 in IMM Domain
This video contains the process to configure disjoint Layer 2 network in Intersight managed UCS domain.
4:17