Use of FQDN Object in Access Policy Firepower Threat Defense
3:27
Description
Related Videos
This is the demonstration on how to use FQDN object in firepower threat defense.
View More
View Less
Related Videos
In Featured Video
-
Play video LTI Mindtree customer story
LTI Mindtree customer story
LTI Mindtree accomplished massive growth, global reach, and 25% fewer IT incidents, powered by Cisco Services.
1:42
-
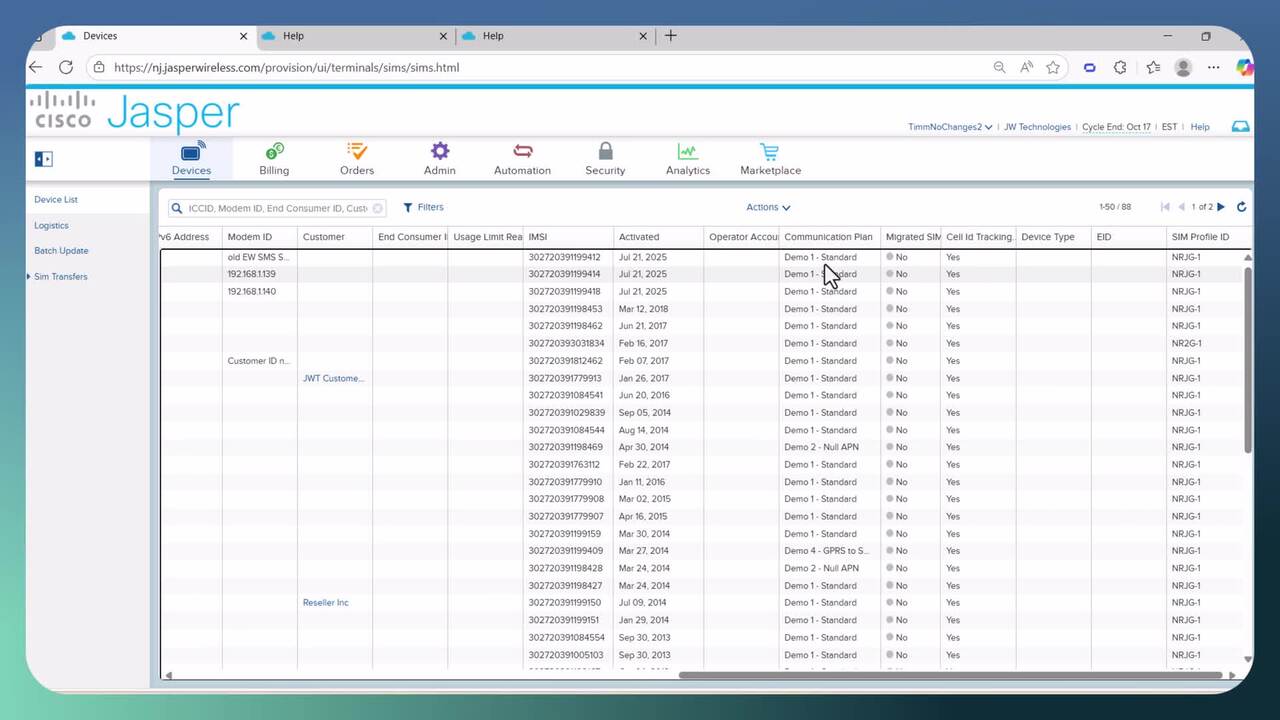
Play video Devices Page
Devices Page
Explanation of the devices page
9:31
-
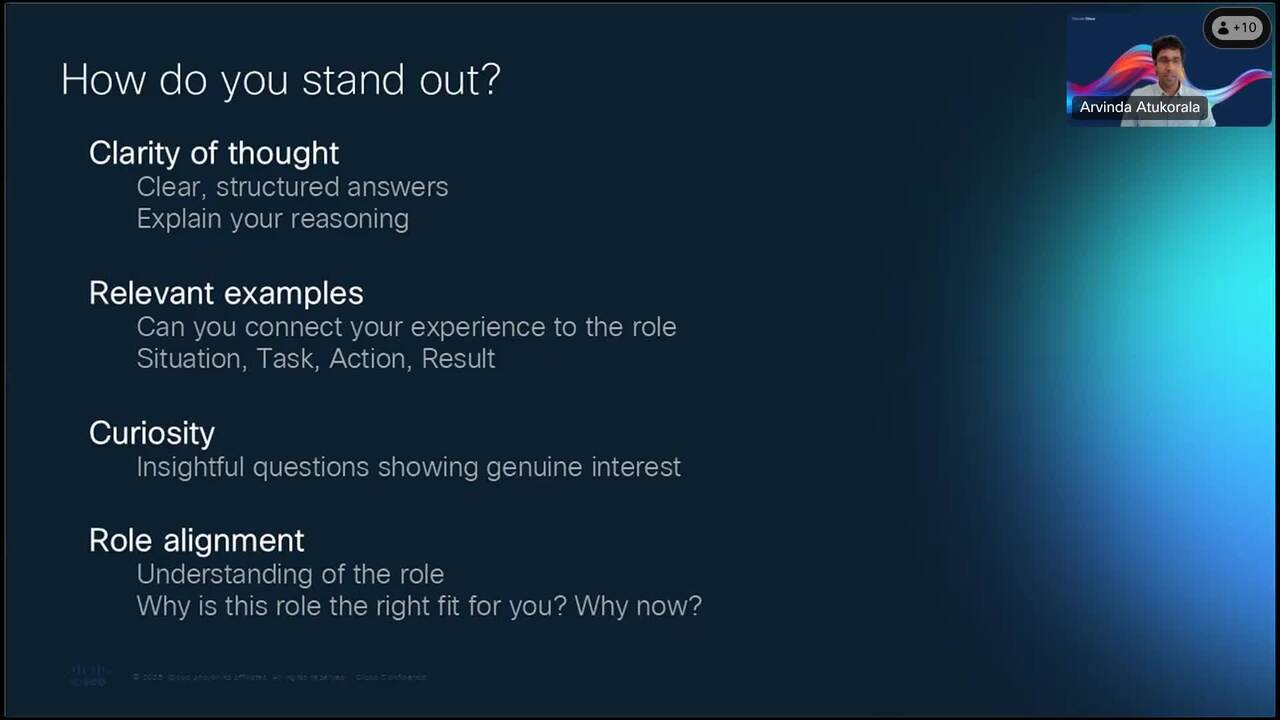
Play video Discover Cisco at a Glance: Ace the Interview
Discover Cisco at a Glance: Ace the Interview
Decode interview formats, prepare for behavioral questions, and learn how to showcase your strengths
56:13
-
Play video The AI Ready Enterprise: Building a Secure Network Architecture for What's Next
The AI Ready Enterprise: Building a Secure Network Architecture for What's Next
Campus networks are under pressure— increased traffic, AI workloads, hybrid work, and a rising tide of IoT devices create unprecedented risks. Simplify and secure your AI-ready infrastructure with scalable, integrated security solutions to deliver a
2:22
-
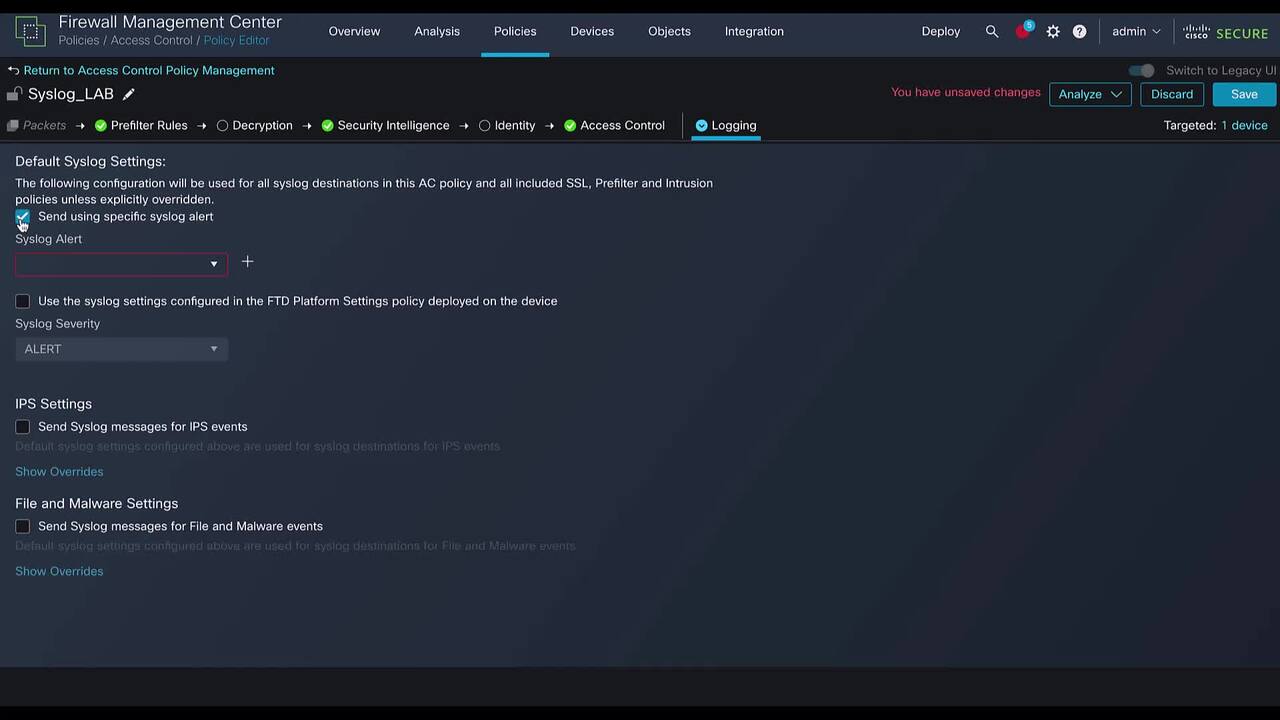
Play video Use alert action to send events to syslog server from FTD
Use alert action to send events to syslog server from FTD
This video demonstrate how to use alert action to send events to syslog server
2:58
-
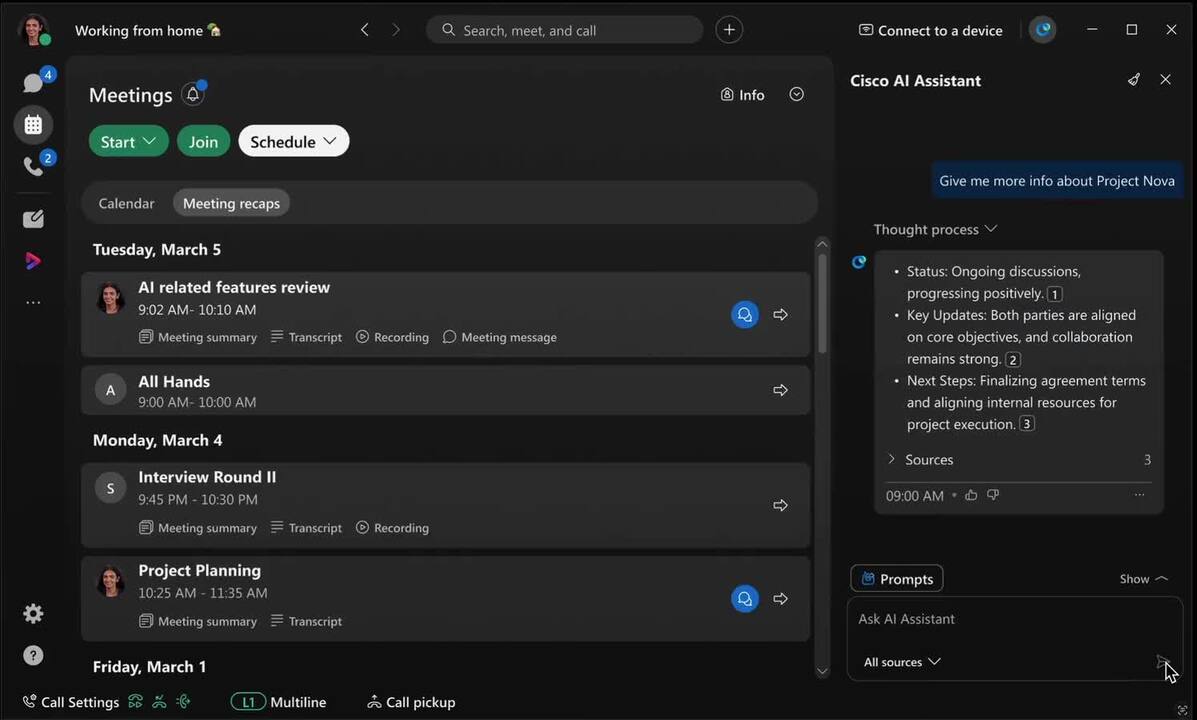
Play video AI Assistant Search with Webex
AI Assistant Search with Webex
AI-Powered Search via Webex AI Assistant
0:16