Spotlight Overview
5:24
Understand the basic features of the Spotlight tool
Related Videos
In Featured Video
-
Play video Desk Pro G2 Demo
Desk Pro G2 Demo
Desk Pro G2 Demo
1:58
-
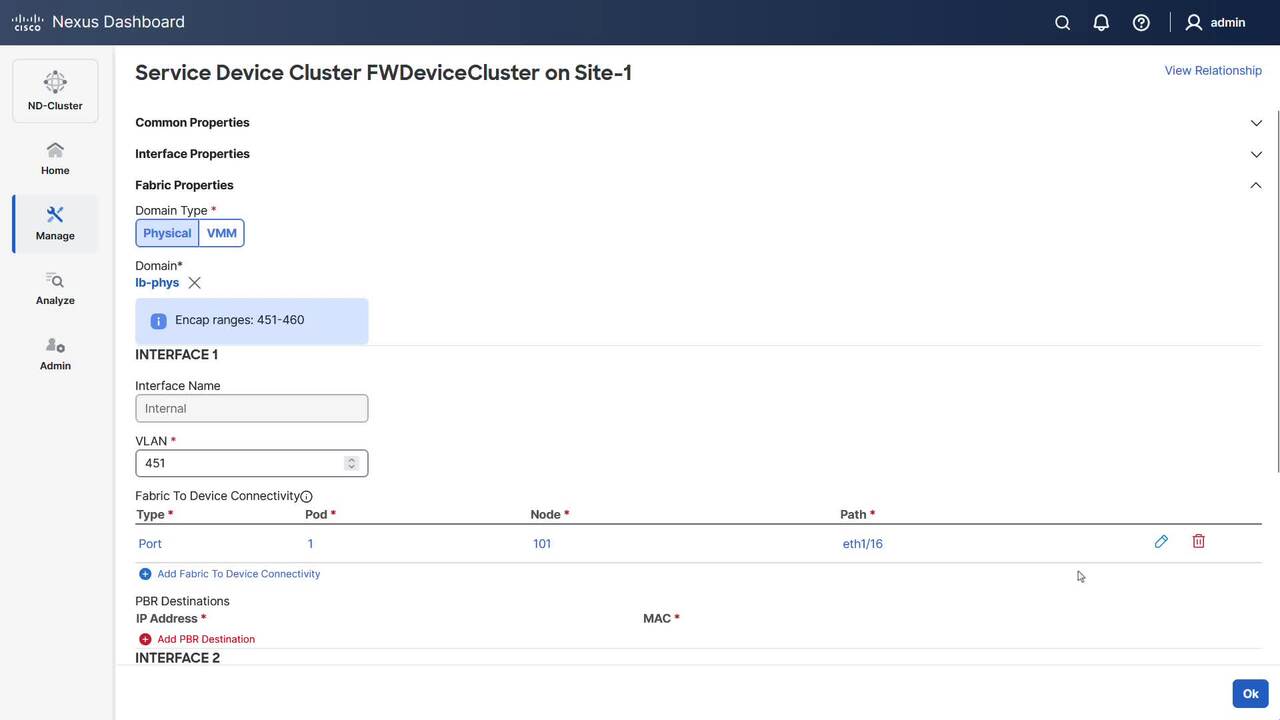
Play video Configure Service Chaining for E-W Traffic in NDO
Configure Service Chaining for E-W Traffic in NDO
This video demonstrates how to configure service chaining in NDO for EPG-to-EPG communication in single site.
6:25
-
Play video Cisco Live EMEA 2026: Driving Smart Grid Innovation - Enedis Scales Operations with Cisco Technology
Cisco Live EMEA 2026: Driving Smart Grid Innovation - Enedis Scales Operations with Cisco Technology
Enedis, a leader in smart grid innovation, has connected over 35,000 substations using the Cisco IR1101, significantly scaling their operations. Hear from Sasan Rostambeik Tafreshi, Senior Advisor at Enedis to learn how they're driving progress.
7:33
-
Play video Cisco Live EMEA 2026: 20/20 Vision into OT Cyber Risks with ZEISS
Cisco Live EMEA 2026: 20/20 Vision into OT Cyber Risks with ZEISS
In factories and roadways, cybersecurity is vital for safety and resilience. Hear from Thrasyvoulos Mystiroudis, Senior Manager, Network and Connectivity at ZEISS on how they're securing production with full visibility into industrial assets.
5:23
-
Play video Cisco at the S4x26 POC Pavilion
Cisco at the S4x26 POC Pavilion
At the S4x26 conference, Cisco was part of the POC Pavilion where Dale Peterson challenged vendors to demonstrate real-world industrial security—live! Cisco's visibility driven network segmentation and OT SOC workflows were highly regarded.
11:20
-
Play video Room Kit Pro G2 Demo
Room Kit Pro G2 Demo
Room Kit Pro G2 Demo
1:22