Cisco Meraki Access Manager: Cloud-Native Zero-Trust
53:07
In this session, we unveil Meraki Access Manager, a new product providing highly-scalable, single pane of glass zero-trust network access controls within the Meraki cloud management platform.
Related Videos
In Enterprise Networks
-
Play video Digital Resilience in the AI Era: IDC on Unified Operational Visibility
Digital Resilience in the AI Era: IDC on Unified Operational Visibility
AI is fragmenting operational data across the stack. IDC explains why digital resilience is a data problem—and what it takes to unify signals for real-time visibility and faster action.
0:39
-
Play video Introduction to Cisco Agentic Workflows
Introduction to Cisco Agentic Workflows
Learn about Cisco Agentic Workflows: our free, AI-driven network automation tool in the Meraki dashboard. Easily automate routine tasks, cut manual errors, and speed up network management with simple, low/no-code, repeatable workflows.
2:42
-
Play video How Crown Castle Achieved 6x Faster Provisioning with Automation
How Crown Castle Achieved 6x Faster Provisioning with Automation
Explore how the Crown Castle team transformed the way they provision and manage infrastructure with Cisco Crosswork Network Automation, dramatically increasing efficiency and providing a foundation for continued innovation as they hone operations.
1:14
-
Play video Under the Hood: Scaling AI infrastructure
Under the Hood: Scaling AI infrastructure
Microsoft’s Deepak Bansal and Cisco’s Will Eatherton discuss the shift to AI-first infrastructure. They explore using DPUs and Sonic to improve network efficiency and cost-per-token, while analyzing the competition between hyperscalers and Neoclouds.
34:45
-
Play video Enterprise Wireless Trends and Insights | ABI Research & Cisco
Enterprise Wireless Trends and Insights | ABI Research & Cisco
Hear insights from ABI Research on the evolving enterprise wireless landscape and what it means for IT and networking leaders. This video highlights key findings from the report and how organizations can prepare for next-generation wireless networks.
5:37
-
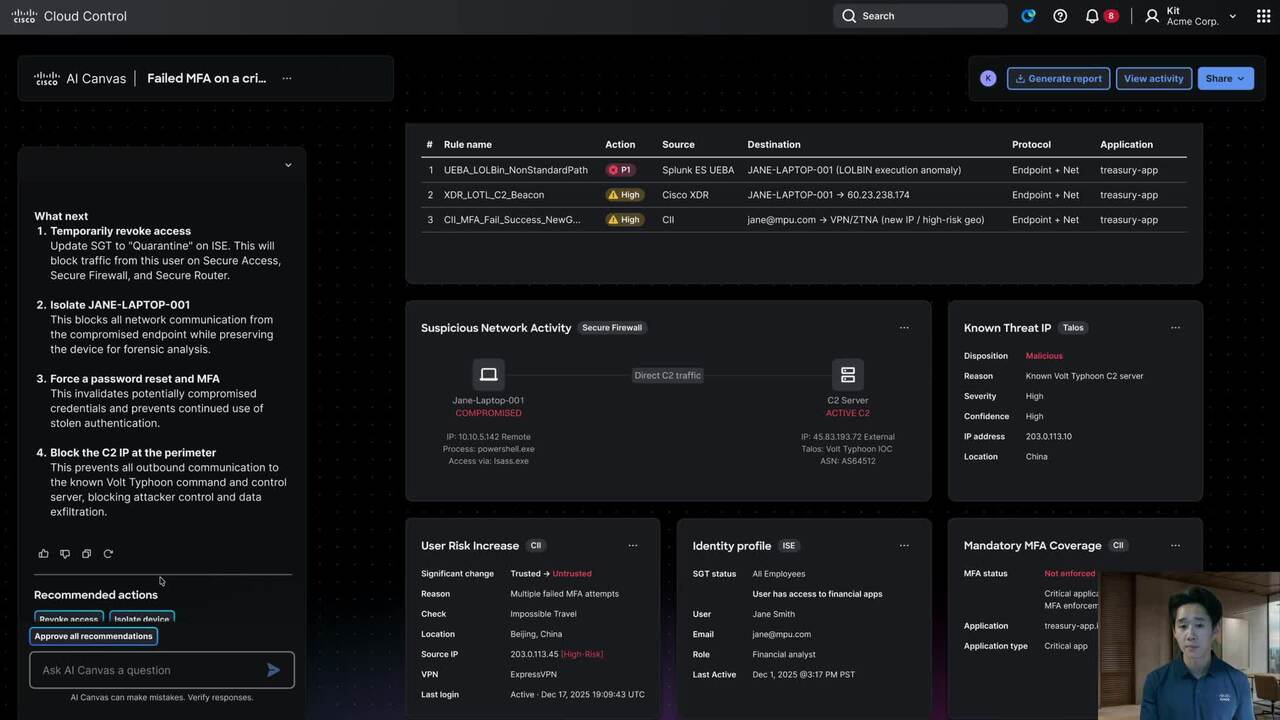
Play video AI Canvas troubleshoots across security and networking domains
AI Canvas troubleshoots across security and networking domains
AI Canvas correlates identity, endpoint, and network signals to detect a Volt Typhoon-style compromise, contain the breach, harden access with MFA and ZTNA, and protect critical financial apps with segmentation and continuous monitoring.
4:10