Security Analytics and Cisco XDR
29:46
This session gives an overview of Cisco Secure Analytics and the newly introduced Cisco XDR.
Related Videos
In Cisco Live
-
Play video Cisco Live Melbourne: Insights from BHP and Cisco Industrial IoT
Cisco Live Melbourne: Insights from BHP and Cisco Industrial IoT
Hear Michelle Fernando, Superintendent OT Networks at BHP and Samuel Pasquier, VP, Product Management, Cisco IloT Networking discuss the latest trends transforming the future of mining.
6:20
-
Play video Interview with TD Synnex about Cisco Secure AI Factory with NVIDIA
Interview with TD Synnex about Cisco Secure AI Factory with NVIDIA
Cisco’s Cassie Roach and Loïc d'Ursel of TD Synnex discuss why TD Synnex is making an investment in the Cisco Secure AI Factory with NVIDIA.
4:10
-
Play video Unlock human potential
Unlock human potential
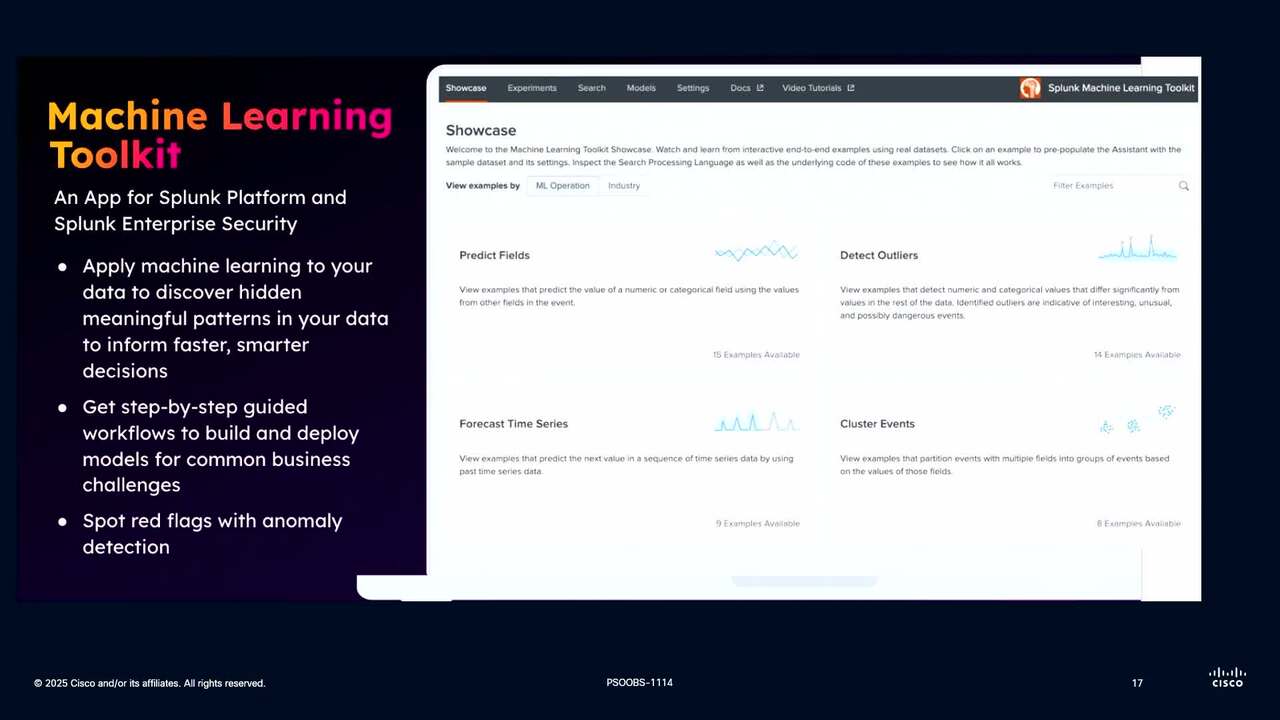
Learn about the Machine Learning Toolkit, AI Assistant for Splunk's SPL, and how we're embedding Splunk AI across our platform.
3:38
-
Play video Interview with World Wide Technology about Cisco Secure AI Factory with NVIDIA
Interview with World Wide Technology about Cisco Secure AI Factory with NVIDIA
Cisco’s Cassie Roach talks with Terry Frost and Nathan Litz of World Wide Technology about why they are making an investment in the Cisco Secure AI Factory with NVIDIA.
6:51
-
Play video Cisco Live EMEA 2026: Preview of Cisco’s AI Networking and AI-Ready Data Center Innovations
Cisco Live EMEA 2026: Preview of Cisco’s AI Networking and AI-Ready Data Center Innovations
Cassie Roach and Alex Pujols explore the latest AI Networking and AI-Ready Data Center innovations, including our new Cisco Silicon One G300 and Cisco Unified Edge, in World of Solutions at Cisco Live EMEA.
9:37
-
Play video CLEMEA: Cassie Roach's Interview with SCC about Cisco Secure AI Factory with NVIDIA
CLEMEA: Cassie Roach's Interview with SCC about Cisco Secure AI Factory with NVIDIA
Cassie Roach and Steve Crompton of SCC discuss why SCC is making an investment in the Cisco Secure AI Factory with NVIDIA.
4:54