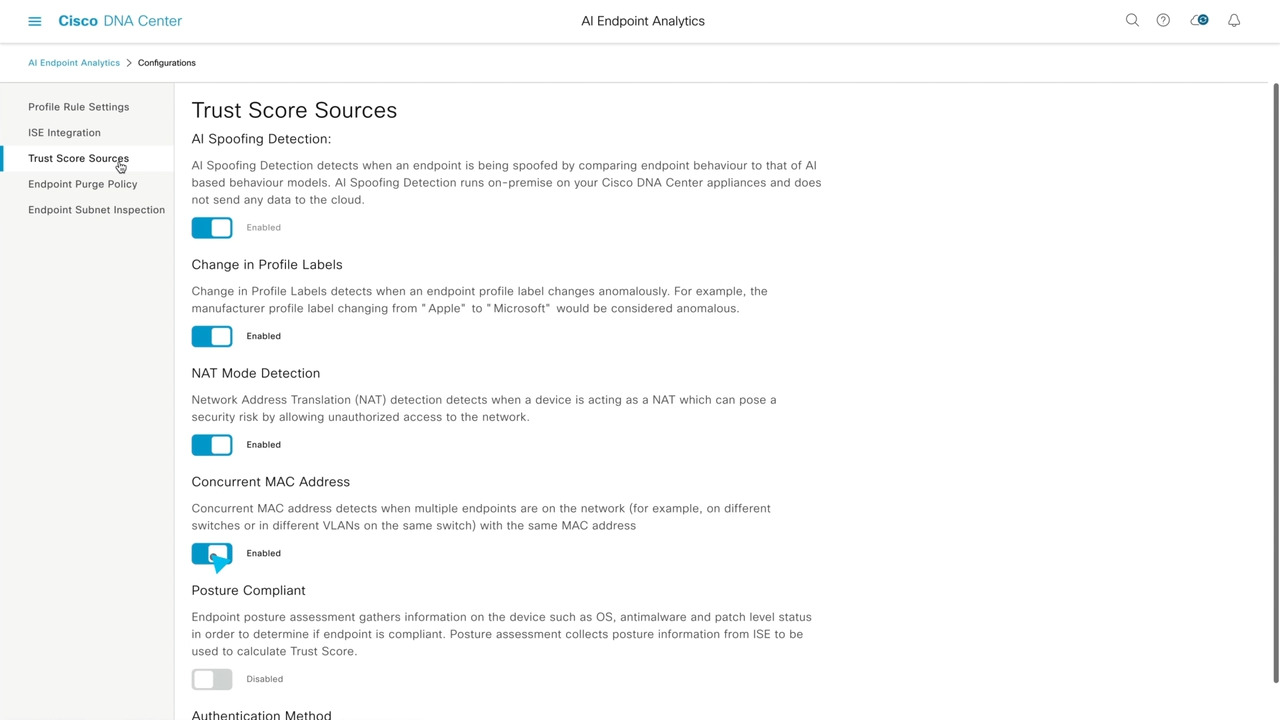
Cisco Catalyst Center Zero Trust Network demo
3:45
See how setting up Cisco Catalyst Center's Zero Trust Networking policies protect your users from threat and to improve overall performance. Learn more at cisco.com/go/dnacenter
Related Videos
For "zero trust"
-
Play video Cisco Identity Services Engine (ISE) leaps into infrastructure as code with ISE 3.1 from the cloud
Cisco Identity Services Engine (ISE) leaps into infrastructure as code with ISE 3.1 from the cloud
See how provisioning ISE from the cloud enables rapid deployment of network accesses and control services to anywhere, automatically extending policy to build zero trust within the workplace without slowing down the business.
1:43
-
Play video Secure Access, Seamless Experience: LTIMindtree Secures Remote Work at Scale
Secure Access, Seamless Experience: LTIMindtree Secures Remote Work at Scale
Watch how this leading global technology consulting company modernizes their zero trust to boost cyber resilience and improve user experience.
3:13
-
Play video ISE 3.0 Demo - Simplifying visibility and control in the zero-trust workplace
ISE 3.0 Demo - Simplifying visibility and control in the zero-trust workplace
ISE 3.0 is here. Take a look at the new UI and see how we are simplifying visibility and compliance with agentless posture and enabling cloud-first strategies. Learn more about ISE: https://www.cisco.com/c/en/us/p
3:48
-
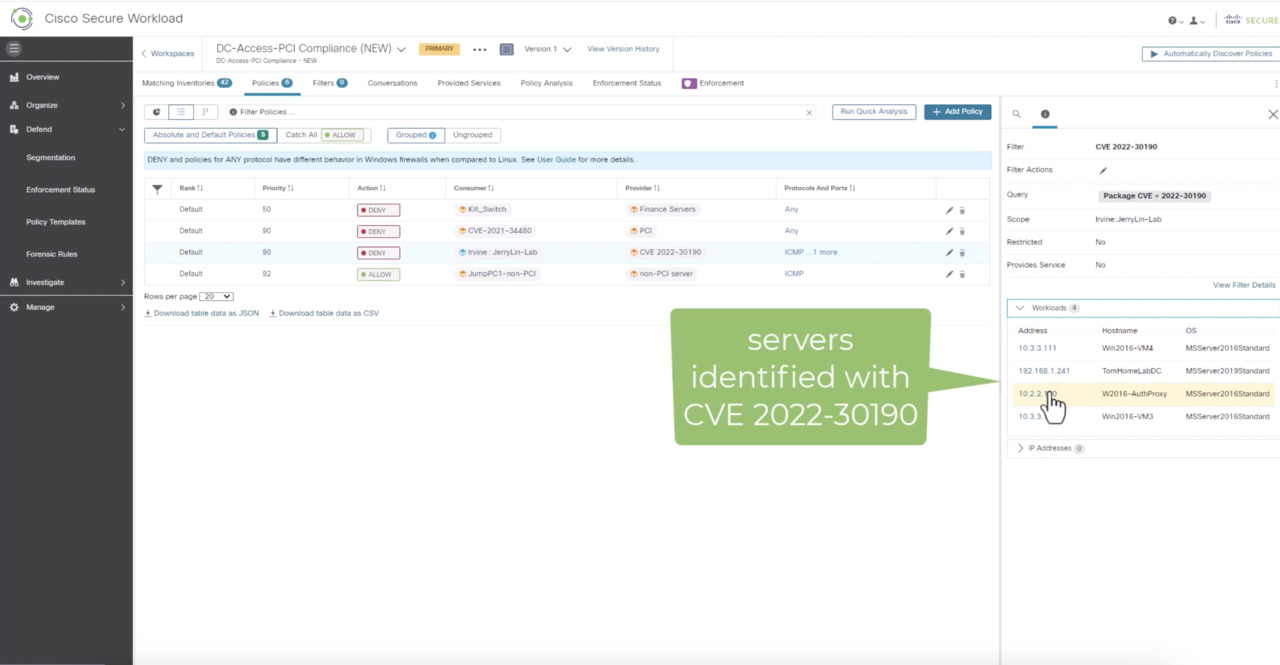
Play video Cisco Zero Trust in Action: Apply micro-segmentation at scale
Cisco Zero Trust in Action: Apply micro-segmentation at scale
This product demo shows how Secure Workload uses vulnerability data to enforce trusted access via micro-segmentation policies. Quite simply, if an app is vulnerable, the policy engine will automatically limit access to it until it can be remediated.
5:36
-
Play video Cisco Trusted Access is a practical Zero Trust approach to security
Cisco Trusted Access is a practical Zero Trust approach to security
Learn the meaning of Zero Trust—one name amongst many—advocating for customers to adopt a trust-centric security approach that complements the threat-centric security solutions we’ve already deployed. Cisco’s answer to Zero Trust is our Cisco Trusted
2:50
-
Play video Cisco Wireless: Zero-Trust How to Demo
Cisco Wireless: Zero-Trust How to Demo
Let's explore rogue management and aWIPS, randomized and changing mac, AI endpoint analytics, and segmentation with Cisco wireless. Learn more at cisco.com/go/wireless
4:15