This is why you will fail: Most successful attack scenarios and their defenses
31:22
Tijmme Gommers (Northwave) - Presentation from SECCON NL 2022
Related Videos
In Security
-
Play video Creating a Zero Trust Environment in DoD
Creating a Zero Trust Environment in DoD
A discussion with Marcos Rogers: Leveraging a Comply to Connect Security Architecture
4:31
-
Play video Cisco Cloud Application Security Overview Video
Cisco Cloud Application Security Overview Video
Do you wish you could monitor, detect, prevent, and dynamically remediate threats from your cloud applications and underlying infrastructure - all from one tool? See how it's possible with Cisco Cloud Application Security.
2:18
-
Play video Cisco Cyber Vision Deployment - Episode 1 - Center OVA Deployment - 4.2.3
Cisco Cyber Vision Deployment - Episode 1 - Center OVA Deployment - 4.2.3
In part one of our Cisco Cyber Vision deployment series, we present an overview of the Cisco Cyber Vision Center and walk through the deployment process of the Cyber Vision Center ova into a VMWare ESXi environment.
10:21
-
Play video Talos March 2024 APJC Update: The Evolution of GhostSec (Social)
Talos March 2024 APJC Update: The Evolution of GhostSec (Social)
In this video Cisco Talos researcher Chetan Raghuprasad discusses a recent surge in activity from the hacker group GhostSec, and how they have evolved their tooling and affiliate program.
0:44
-
Play video Talos March 2024 APJC Update: The Evolution of GhostSec
Talos March 2024 APJC Update: The Evolution of GhostSec
In this video Cisco Talos researcher Chetan Raghuprasad discusses a recent surge in activity from the hacker group GhostSec, and how they have evolved their tooling and affiliate program.
9:42
-
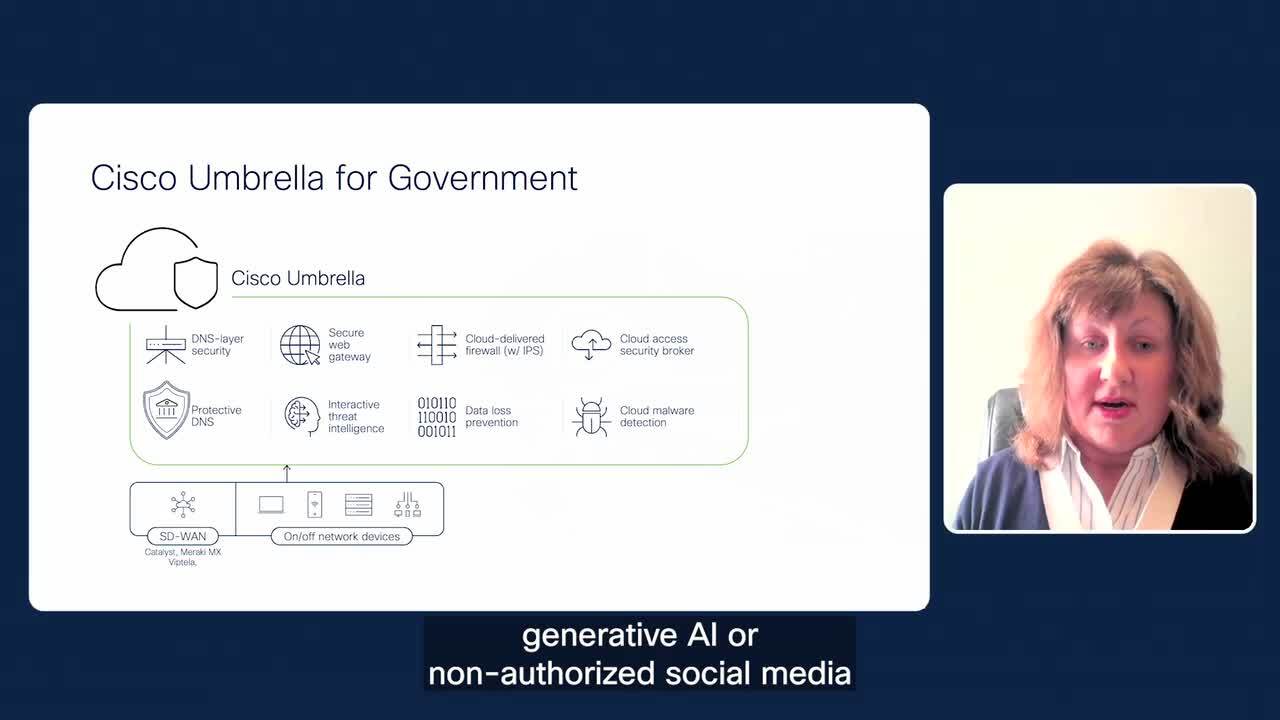
Play video Cisco Umbrella for Government
Cisco Umbrella for Government
Learn about cyber threat defense for government agencies to protect remote offices and hybrid workers.
2:19