Creating a Zero Trust Environment in DoD
4:31
A discussion with Marcos Rogers: Leveraging a Comply to Connect Security Architecture
Related Videos
In Security
-
Play video Risk Based Endpoint Security with Cisco Vulnerability Management and Cisco Secure Endpoint
Risk Based Endpoint Security with Cisco Vulnerability Management and Cisco Secure Endpoint
Cisco Vulnerability Management integrates with Cisco Secure Endpoint to ingest endpoint vulnerability data, enabling users to detect, assess, prioritize, and manage endpoint vulnerabilities with a data science-driven approach.
1:33
-
Play video Cisco AI Assistant in XDR
Cisco AI Assistant in XDR
A generative AI-powered assistant embedded within Cisco XDR that empowers SOC analysts of all levels with the information they need to make critical decisions quickly.
1:30
-
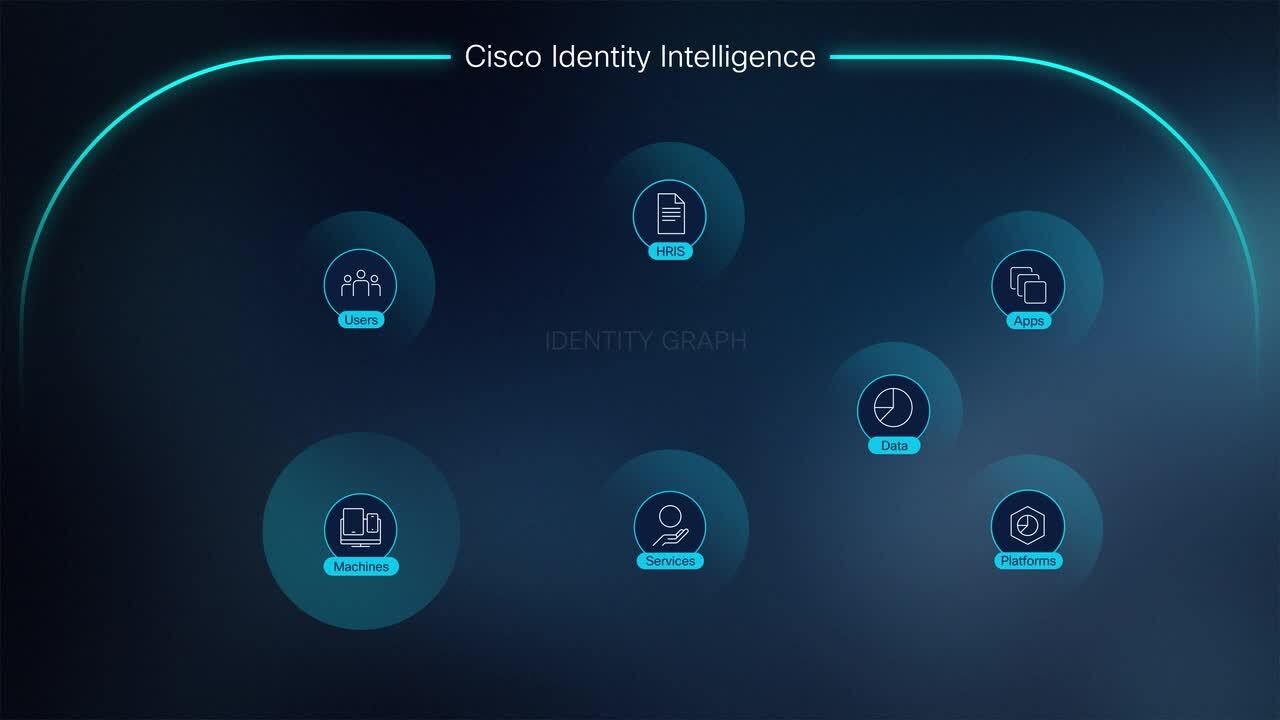
Play video Cisco Identity Intelligence
Cisco Identity Intelligence
Identity-based attacks hit companies across all industries as attackers are able to simply "log on." Cisco Identity Intelligence is built to solve the disconnect between user authentication and access. Learn more.
2:08
-
Play video Talos March 2024 APJC Update: The Evolution of GhostSec
Talos March 2024 APJC Update: The Evolution of GhostSec
In this video Cisco Talos researcher Chetan Raghuprasad discusses a recent surge in activity from the hacker group GhostSec, and how they have evolved their tooling and affiliate program.
9:42
-
Play video Cisco Umbrella for Government
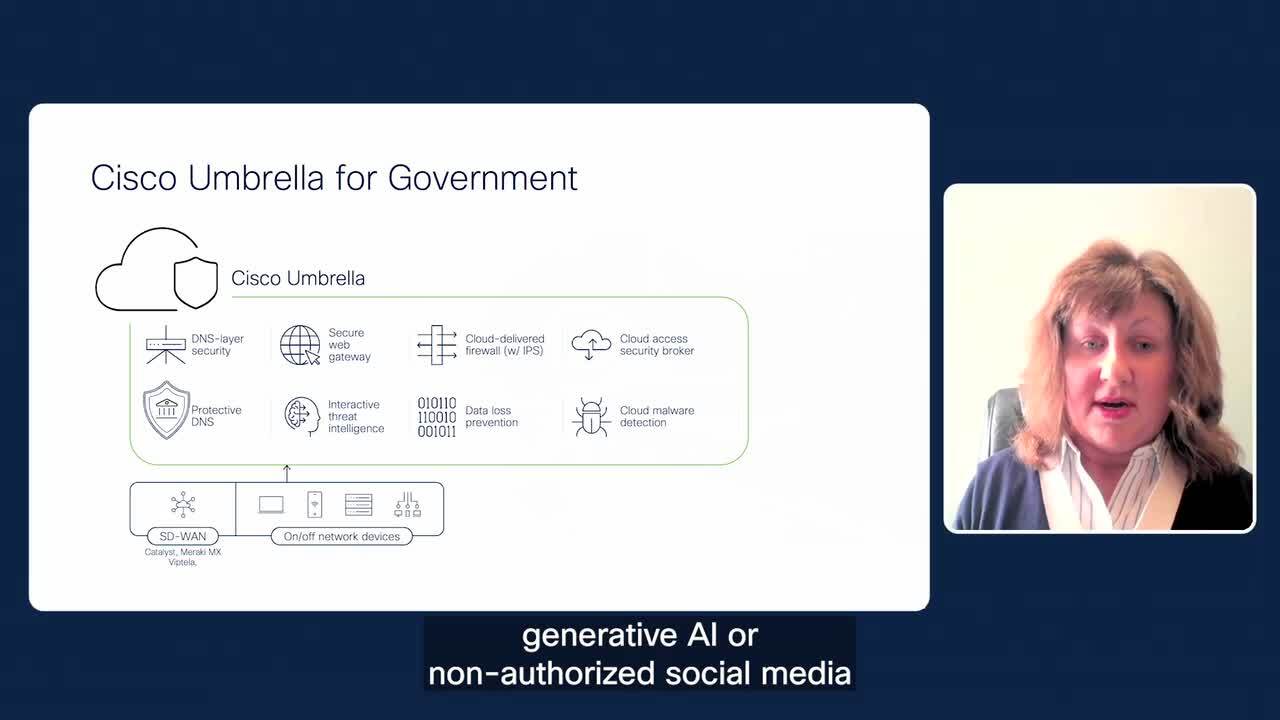
Cisco Umbrella for Government
Learn about cyber threat defense for government agencies to protect remote offices and hybrid workers.
2:19
-
Play video Cisco Cloud Application Security Overview Video
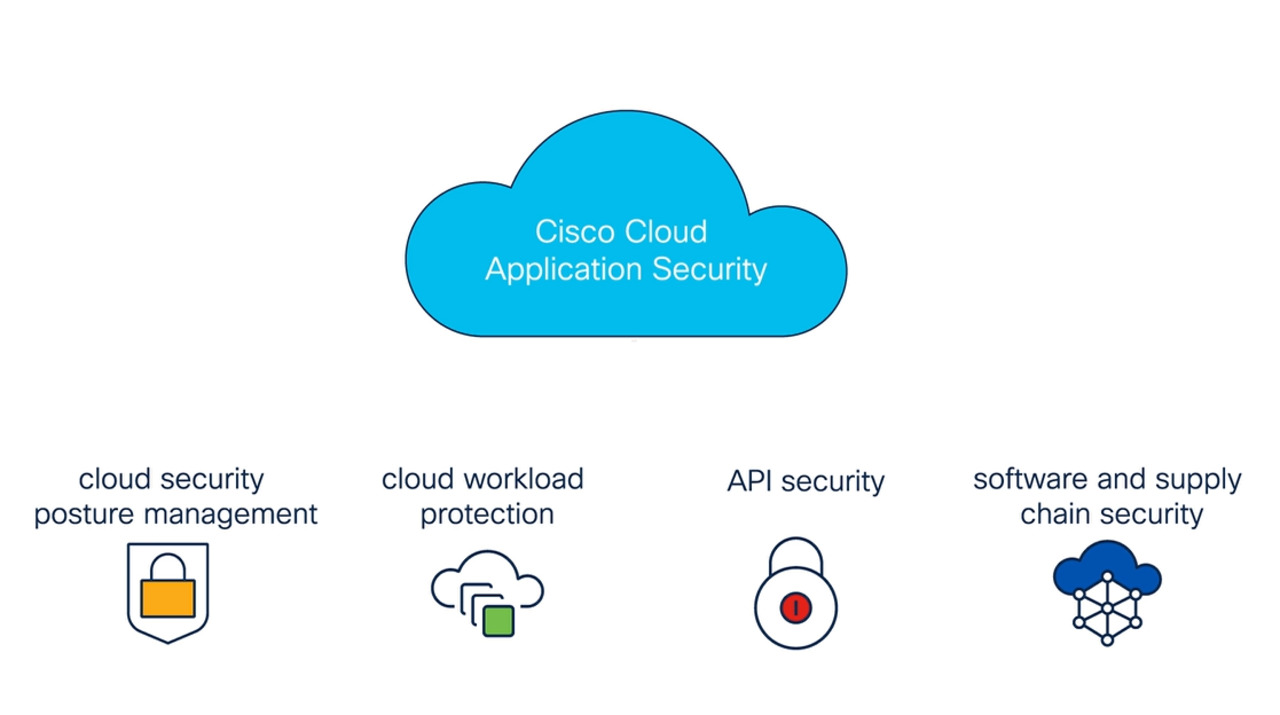
Cisco Cloud Application Security Overview Video
Do you wish you could monitor, detect, prevent, and dynamically remediate threats from your cloud applications and underlying infrastructure - all from one tool? See how it's possible with Cisco Cloud Application Security.
2:18