-
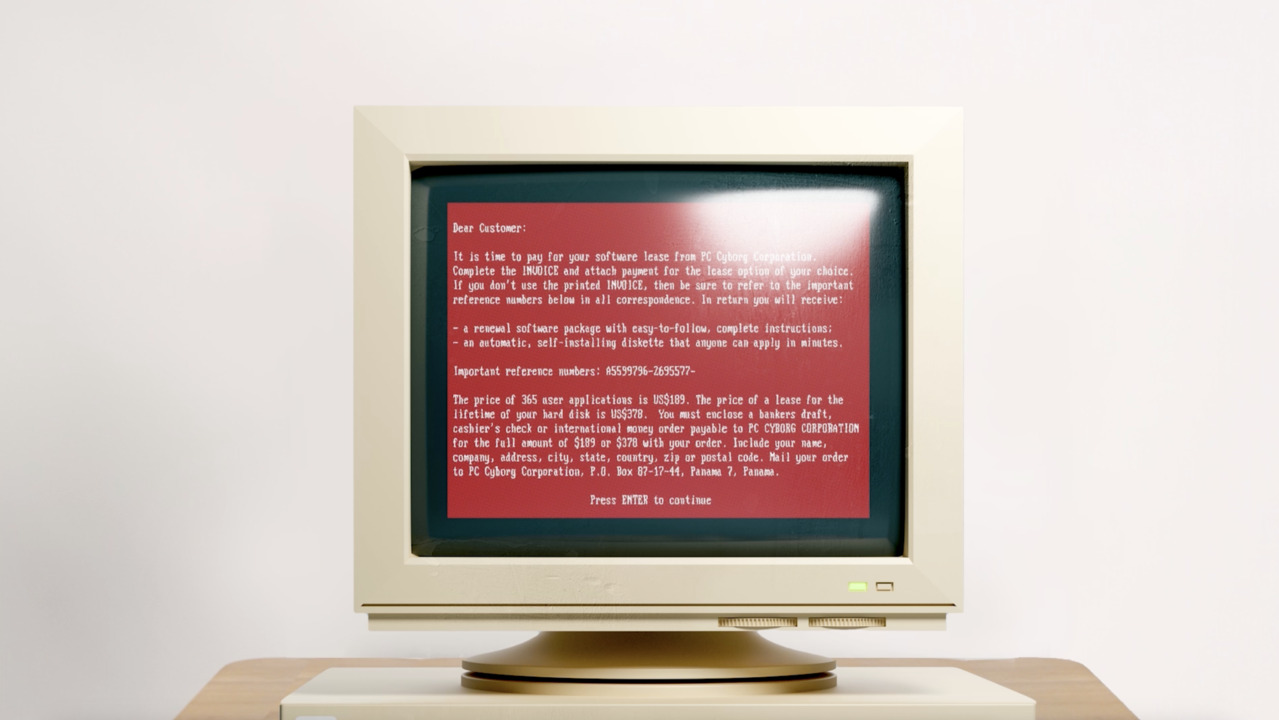
The Future of Ransomware: Inside Cisco Talos Threat Hunters
See how Cisco Talos threat hunters identify new and evolving ransomware threats in the wild, and how their research and intelligence helps organizations build strong defenses.
8:03
-
How Hybrid Should Work
Making hybrid work, work better for everyone. Explore Cisco solutions at www.cisco.com/go/hybridwork
0:30
-
Talos IR On Air: Reviewing top threats of Q1 2023
Cisco Talos Incident Response recaps our latest Quarterly Trends Report. The panel discusses the top ransomware families, new tactics that attackers are using, and the industries that are most at risk.
32:28
-
What is observability
In modern technology environments, observability is a process that uses software tools to detect issues by observing both the inputs and outputs of the technology stack. See how Cisco view observability.
1:58
-
APIClarity Blog Series Introduction
This video introduces two new blog series on APIClarity: an overview series for the basics, and a how-to series to walk through the functionality.
1:46
-
How Hybrid Should Work
The best work experiences empower everyone. Connect and protect your teams, accelerate their productivity, and watch them thrive with hybrid work solutions. Making hybrid work, work better for everyone. Explore Cisco solutions at cisco.com/go/hybrid
1:03
-
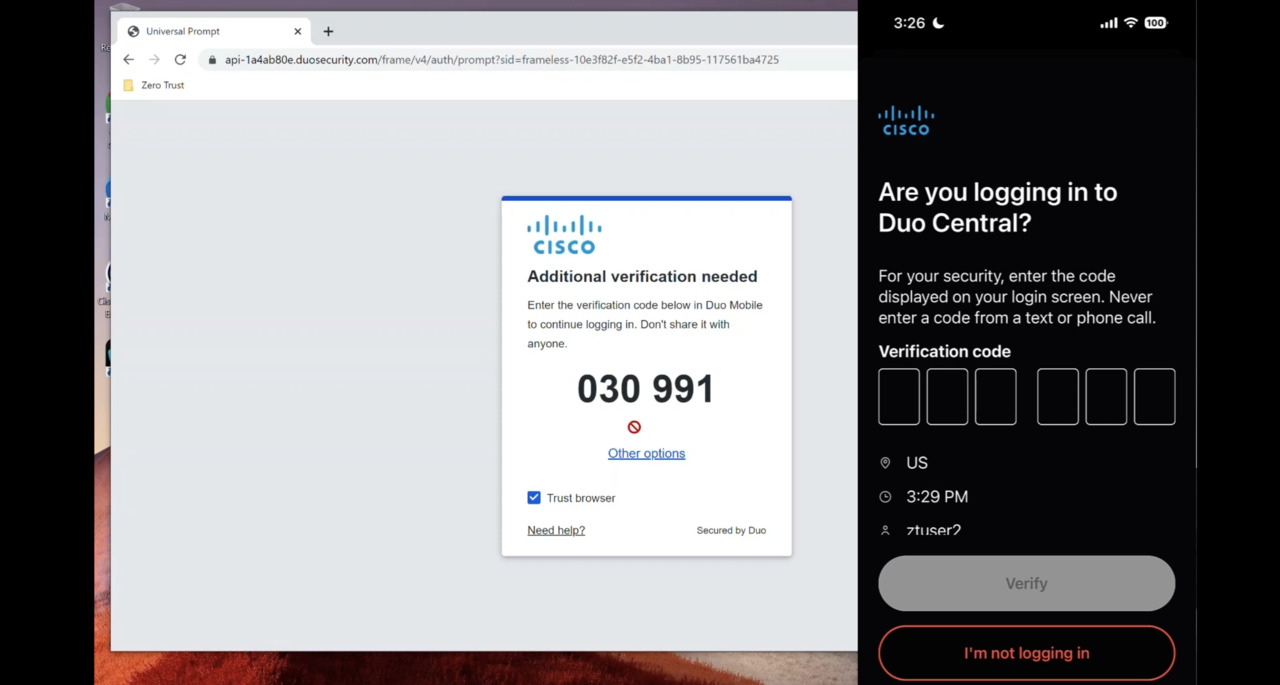
Cisco Zero Trust in Action: Secure user access to applications
This product demo shows a day in the life of a user gaining secure remote access to applications by continuously verifying user and device trust using Cisco zero trust technologies such as Duo and Umbrella.
7:40
-
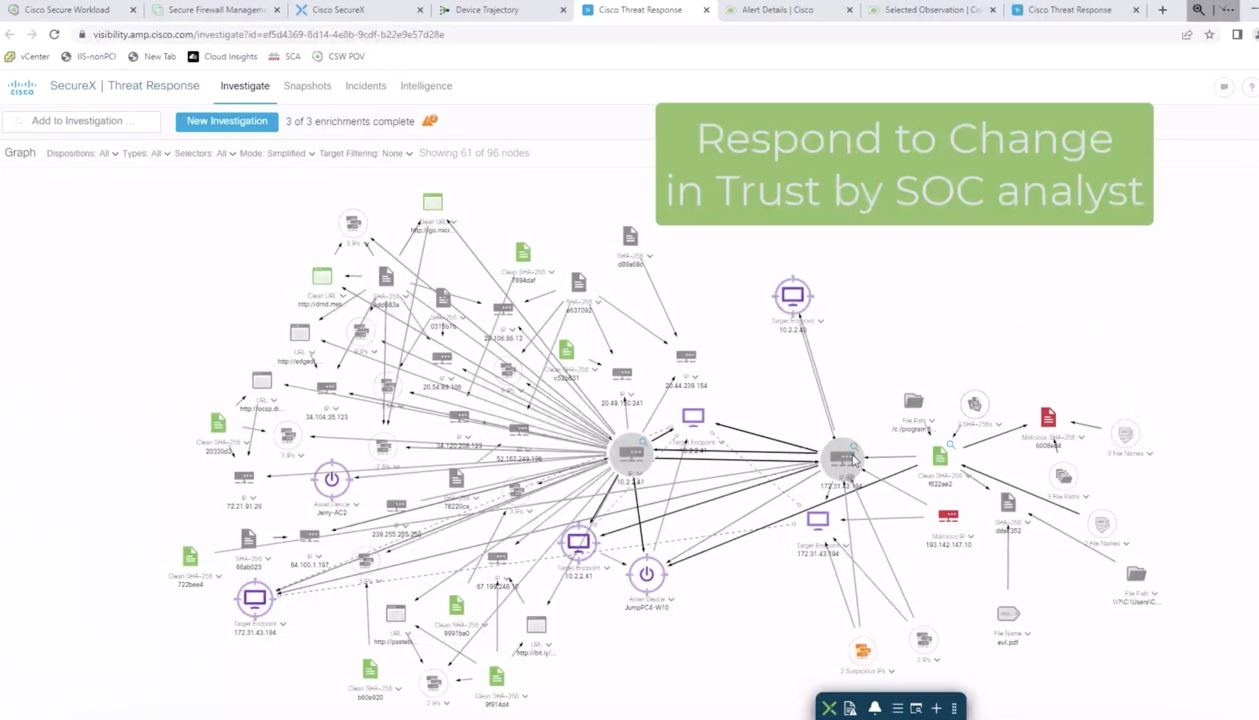
Zero Trust in Action: Automate and orchestrate security workflows
This product demo shows how Secure Workload together with Secure Firewall allows for quick detection and response to a compromised AWS server via the automated and orchestrated workflows in SecureX. Rapid response is key for zero trust security.
5:59
-
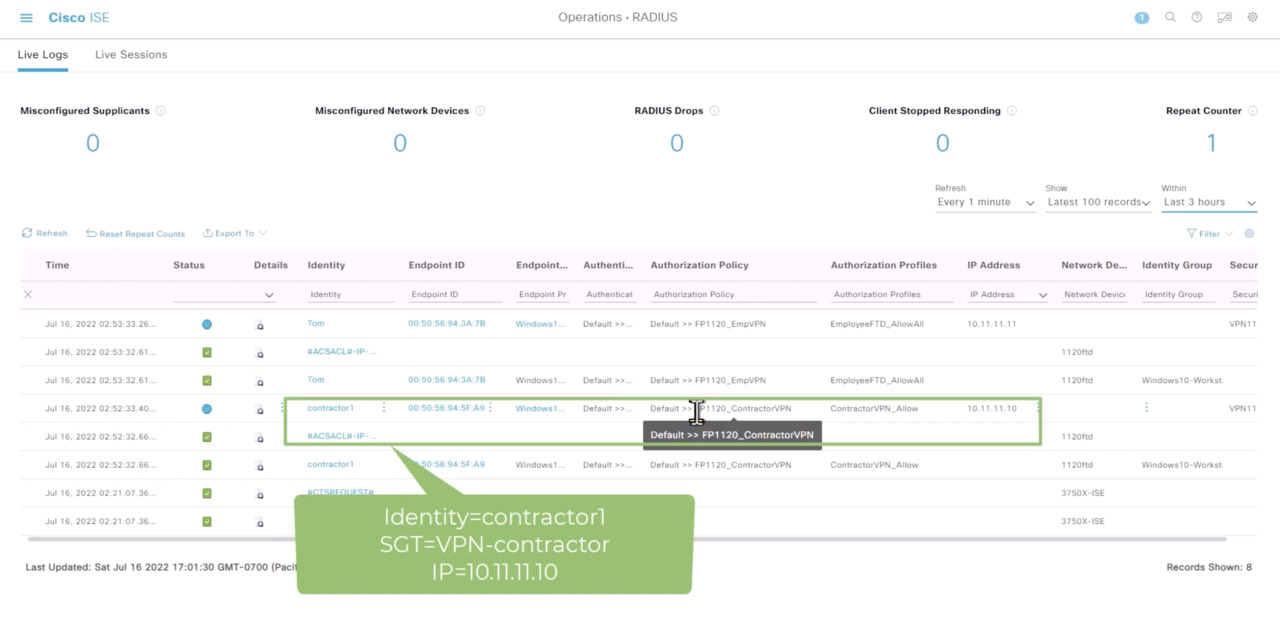
Cisco Zero Trust in Action: Unify access policy across networks and clouds
This product demo shows how ISE uses Security Group Tags (SGTs) to establish trust and enforce trust-based access based on user type (employee vs. contractor) and then integrates this with the Secure Workload access policy for zero trust security.
7:42
-
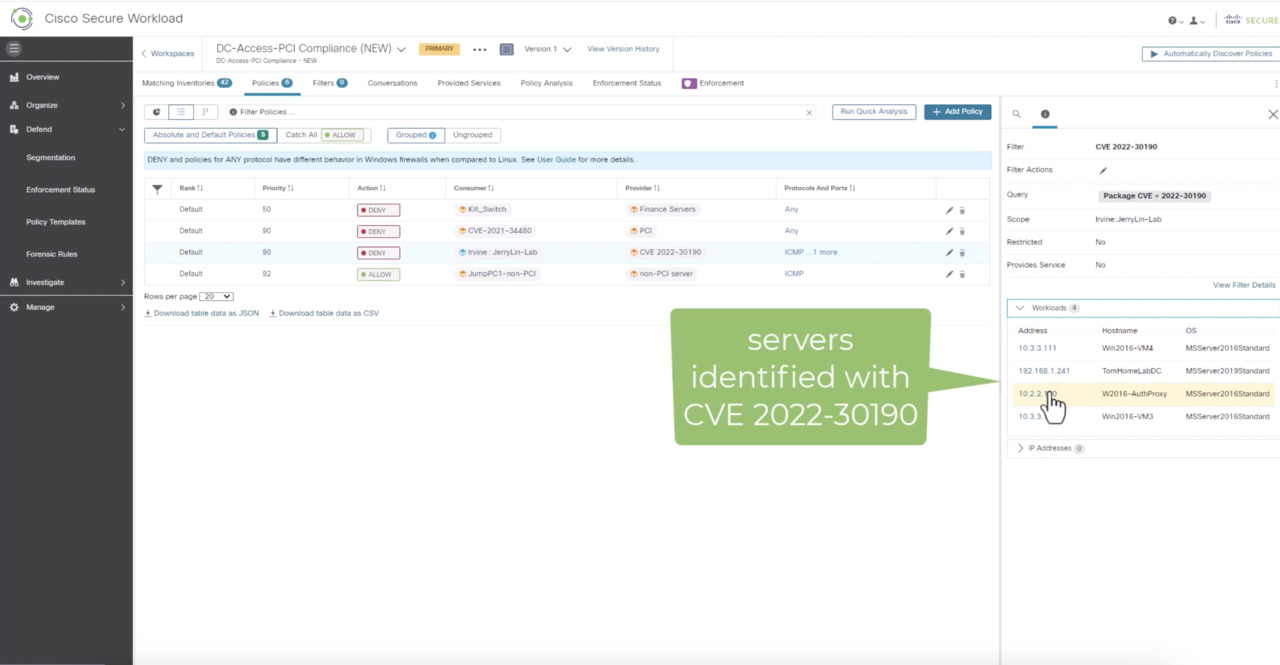
Cisco Zero Trust in Action: Apply micro-segmentation at scale
This product demo shows how Secure Workload uses vulnerability data to enforce trusted access via micro-segmentation policies. Quite simply, if an app is vulnerable, the policy engine will automatically limit access to it until it can be remediated.
5:36
-
Analytics and Automation: Driving SD-WAN Success at the Network Edge (Audio Only)
Listen to this podcast episode to learn how Cisco SD-WAN solutions utilize network analytics and automation to simplify tasks and decrease risks associated with digital infrastructure management.
15:47
-
Cisco Catalyst 9100 Access Points product video
Cisco Catalyst 9100 Access Points product video
1:22
- Load More
Cisco Video Portal


Share this video
Embed
Size: x pixels